Results of the EU funded research & development project: “JURAND – National Quantum Random Number Generator” (Contract no. POIR.01.01.01-00-0173/15)
The page summarizes results of the “JURAND – National Quantum Random Number Generator” project contracted by the National Research & Development Center and implemented since 2015. The project includes industrial research and development activities aimed at creating within national technology and commercializing of a quantum truly random number generator, that produces randomness based on a fundamentally non-deterministic quantum-mechanical process. R&D activities will lead to creation of a hardware, that will provide a source of truly (non-deterministic in a physical sense) random numbers basing on fundamental laws of quantum mechanics, with two significant features: 1) performance necessary for practical cryptographic applications within streaming communications (above 1 Mbit/s), and 2) fully open technical specifications instead of a “black box” architecture, that would theoretically allow for a programmed determinism of generated output in the form of deviation, conditional pattern or control (i.e. a “trojan horse” in critical components of cryptographic systems utilizing non-transparent systems from external suppliers). This turned out to be the case, on the occasion of the NSA abuse scandal disclosed in 2014 by Snowden, within all chips from Intel and RSA companies – leaders of IT security industry – in order to provide the NSA with the ability to rapidly break asymmetric cyphers widespread throughout the Internet, e.g. RSA, for which the so called initialization vectors that condition the cipher’s computational complexity, are random strings.Stage 1:
Stage 1 of the “JURAND – National Quantum Random Number Generator” project was carried out on industrial research in the field of a random sequence verification model generated in quantum processes. The main result of this research was the invention of a new concept of a publicly owned quantum random number generator to verify the randomness of a quantum generated sequence without revealing its confidential form, which is a fundamental and qualitatively innovative theoretical result regarding the definition of the quantum randomness verification model planned in stage 1. This is a very significant conceptual contribution to the scope of the results so far on the engineering of randomness generation on an international scale. This concept was described in the form of a scientific publication (P-1) and sent to the international scientific periodical “Entropy” on November 1, 2017, and also submitted for patent protection under the national procedure at the Patent Office of the Republic of Poland, UPRP and international procedure under the Patent Cooperation Treaty (PCT) to the World Intellectual Property Organization (WIPO) in Geneva (patent applications ZP-1 and ZP-2, respectively). The report (R-1) contains a detailed substantive report on the results of research work on the implementation of stage 1 of the project. As part of the results of the research work carried out, the contractor issued the following publications: R-1: Report on the implementation of industrial research under stage 1 of the project, entitled “JURAND – National Quantum Random Number Generator” (milestone in the implementation of stage 1 of the project) P-1: Publication in English in the international scientific journal Entropy, entitled “Quantum random number generator protocols based on topologically inequivalent entanglements of quantum states” [Entropy – Open Access Journal, ISSN 1099-4300; CODEN: ENTRFG, MDPI]) P-2: publication in English on the international online quantum security platform “seQre.net”, entitled “Randomness” P-3: publication in English on the international online quantum security platform “seQre.net”, entitled “Random numbers generator statistical tests” ZP-1: Patent application in Polish (national URPP procedure), entitled “Entangled Quantum Random Number Generator with public certification of randomness” (report number: P.424140 of 30.12.2017) ZP-2: Patent application in English (international PCT procedure), entitled “Entanglement Quantum Random Number Generator with public randomness certification” (application number: WIPO ST 10/CPL424140 of 31.12.2017) W-1: Source and statistical data in the scope of conducted randomness analyzes of laboratory-generated stringsStage 2:
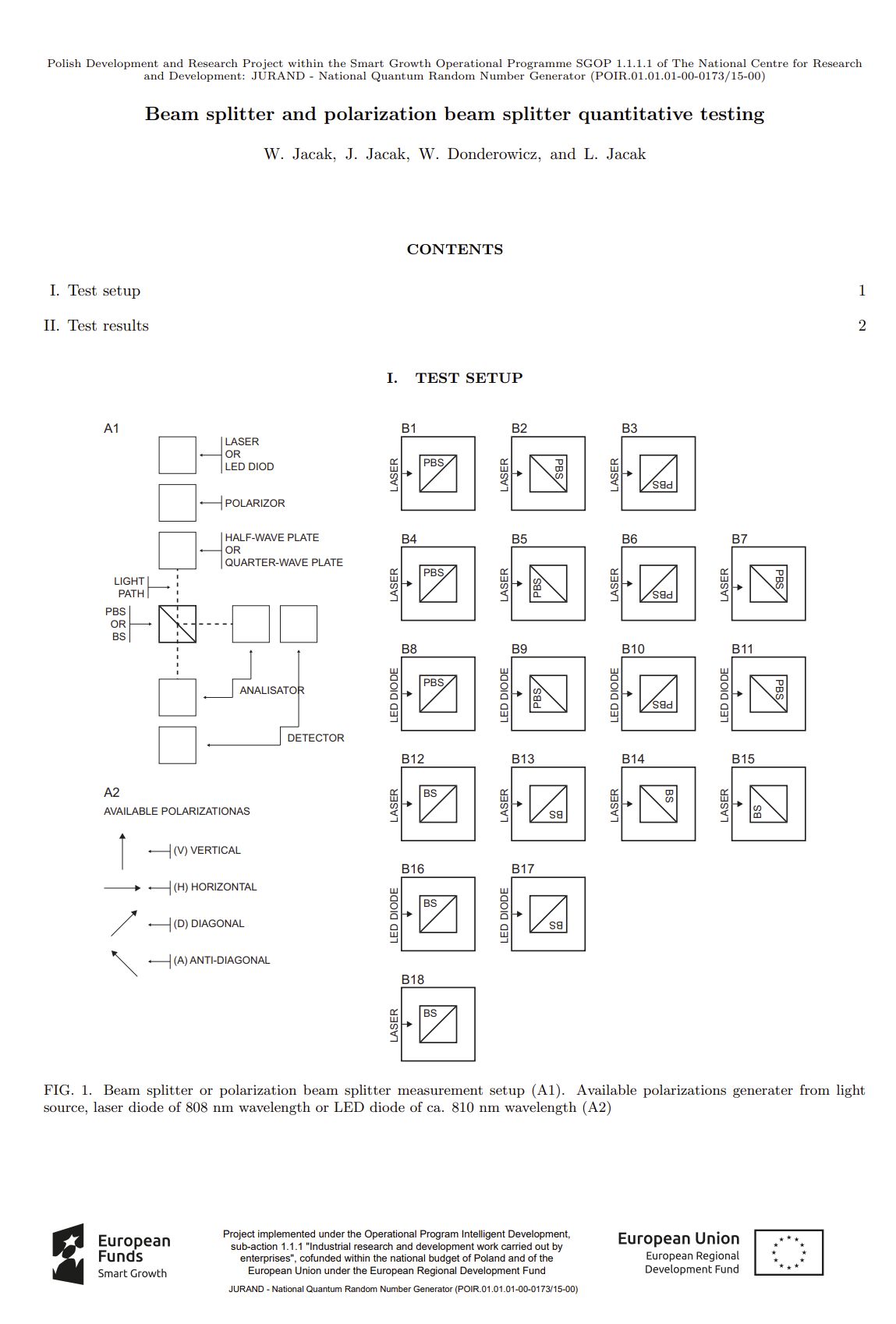
This section summarizes the results of the research work carried out under the stage 2 of the project. Full summary is contained in the document “R-2: Report on implementation industrial research under stage 2 of the project ”, which is a milestone in the implementation of this stage 2 of the project and can be found below. The subject of the implementation of the stage 2 of the project was the study of quantum processes for the purpose of generating random numbers in a range characteristics of their quantum dynamics and the nondeterminism of physical mechanisms in a regime of laws quantum mechanics in order to select the most optimal and most effective of them for use in prototyping a truly random quantum number generator. The issue of selecting the most optimal quantum processes to be carried out in stage no 3 project of further prototype work on a practical domestic quantum number generator randomization is multifaceted and covers both aspects of the implementation difficulty of the same quantum processes, so that they implement the given dynamics as close as possible to the theory (i.e. minimizing implementation deviations from quantum nondeterminism), as well as to make these systems remain as simple as possible in terms of design for their miniaturization optimization and cost towards achieving integrated components while ensuring practical levels of technical parameters of the generation rate of binary random sequences and reliability. R-2: Report on the implementation of industrial research under stage 2 of the project, entitled “JURAND – National Quantum Random Number Generator”, a milestone in the implementation of stage 2 of the project P-4: Publication in Polish on the seQre.net online quantum cryptography commercialization platform, entitled “Analysis of entropy sources for quantum randomness”, which discusses the results of research on quantum effects that can be a source of random sequence generation in order to determine the most optimal sources for empirical laboratory research on the characteristics of sources of randomness P-5: Publication in Polish on the seQre.net online quantum cryptography commercialization platform, entitled “Visualization of the results of empirical research on quantum processes determined as a result of industrial research as the most optimal for the generation of truly random numbers, based on exemplary samples of random binary sequences generated in a laboratory as part of the above-mentioned quantum processes “ P-6: Publication in English on the seQre.net online quantum cryptography commercialization platform, entitled “Beam splitter and polarization beam splitter quantitative testing” P-7: Publication in Polish on the seQre.net online quantum cryptography commercialization platform, entitled “Verification of the non-classical result of breaking Bell’s inequality for entangled states (breaking the limits of classical statistics in entanglement correlations) as a fundamental test of quantum randomness” P-8: Publication in English in the international scientific journal Scientific Reports of the Nature Springer publishing house, entitled “Quantum random number generators with entanglement for public randomness testing”, January 13, 2020, Scientific Reports, Nature Springer
https://www.nature.com/articles/s41598-019-56706-2 (p8-sci-rep -2020-qeqrng.pdf) – the publication was ranked 5th in the ‘Top 100 in Physics’ collection in 2020 in the Scientific Reports (Nature Springer) journal [https://www.nature.com/collections/ihggebhehd]; IF 4.379, list of journals of the Ministry of Science and Higher Education of February 9, 2021. no. 18271, 140 points;
P-9: Publication in English in the international scientific journal Scientific Reports of the Nature Springer publishing house, entitled Quantum generators of random numbers with Supplementary Information, August 9, 2021, Scientific Reports, Nature Springer
https://www.nature.com/articles/s41598-021-95388-7 (p9-sci-rep-2021-qrngSI.pdf and p9-scirep-2021-qrng-corrected-nobib.pdf) – also presenting the partial results of stage 3 of the project in the field of prototyping the QRNG system; IF 4.379, list of journals of the Ministry of Science and Higher Education of February 9, 2021. no. 18271, 140 points;
https://seqre.net/sites/default/files/resources/generic/jurand/P-9-sci-rep-2021-qrng.pdf; – https://seqre.net/sites/default/files/resources/generic/jurand/P-9-sci-rep-2021-qrngSI.pdf
P-10: publication in Polish on the seQre.net online quantum cryptography commercialization platform, entitled “Supplementary expertise in the field of research in terms of theory of mechanics and quantum informatics on the properties of sequences of truly random numbers generated in the course of quantum phenomena and theoretical-experimental research in the field of quantum mechanics and computer science in the field of selected quantum processes that can be used to generate truly random numbers”, presenting also the partial results of stage 3 of the project in the field of prototyping the QRNG system
P-11: publication in Polish on the seQre.net online quantum cryptography commercialization platform, entitled “Data acquisition system for quantum random number generators”, also presenting the partial results of stage 3 of the project in the field of prototyping the QRNG system
P-12: publication in Polish on the seQre.net online quantum cryptography commercialization platform, entitled “Application of an optical trap to a random number generator”, also presenting the partial results of stage 3 of the project in the field of QRNG prototyping
P-13: publication in English on the seQre.net online quantum cryptography commercialization platform, entitled “Random Quantum Noise Generation Using Shot Noise in Semiconductors”, also presenting the partial results of stage 3 of the project in the field of QRNG prototyping
P-14: publication in Polish on the seQre.net online quantum cryptography commercialization platform, entitled “Cryptographic random number generation using shot noise”, also presenting the partial results of stage 3 of the project in the field of QRNG prototyping
P-15: Indirectly related to design research, an English-language publication in the form of the monograph “Quantum Nano-Plasmonics” published in 2020 by Cambridge University Press, in which a member of the project research team (WA Jacak) analyzes quantum effects in nano- plasmonics in the originally developed RPA theory in nanoparticles, the scale of which, however, in relation to the energy of plasmon dynamics turns out to be so small (e.g. the spill-out effect, i.e. quantum pouring out of the electron fluid outside the particle) that it minimizes the possibility of their practical use for generation randomness in single plasmonic nanoparticles; although in integrated systems potentially based on metal-doped nano-particles semiconductor diodes showing a strong plasmonic enhancement of the photoelectric effect in the absorption of photons incident on the semiconductor the situation is more favorable (this plasmonic effect is quantum and easily measurable), the conditions of this process do not allow on the implementation of a practical source of random number generation (the biggest problem here is the excitation of the plasmon in the nanoparticle in a quantum manner, because the energy of the plasmon, i.e. collective vibration of the electron fluid, does not correspond to the energy scale of individual photons falling on the plasmonically modified photodiode, which are the determinants of the quantum randomness of the source modeled by statistics according to Poisson distribution) – for this reason the physical mechanism of nano-plasmonic amplification of the photoelectric effect for the generation of quantum randomness has not been determined as the most optimal for the use of and in the QRNG generator (although the quantum effects of coupling plasmons with band electrons are dominant and implemented according to Fermi golden rule, and due to the ease of measurement of photovoltaic effects, such phenomena could be treated as prospective potential sources of entropy for QRNG using quantum non-determinism of transitions according to Fermi’s golden rule) – these issues are developed in detail and originally in the monograph – August 2020
P-16: (poster; international range), Quantum random number generators with entanglement for public randomness testing, QCrypt 2020 (QCrypt 2020 conference, 10-14 August 2020, online conference)
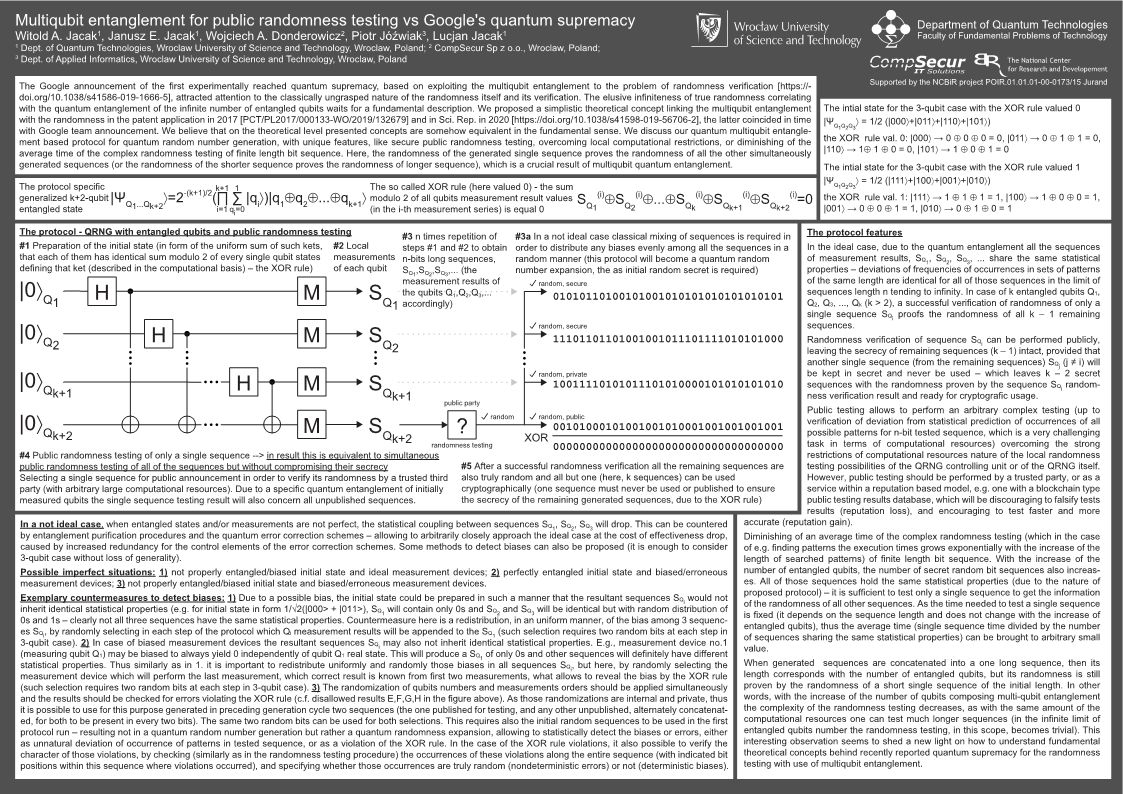
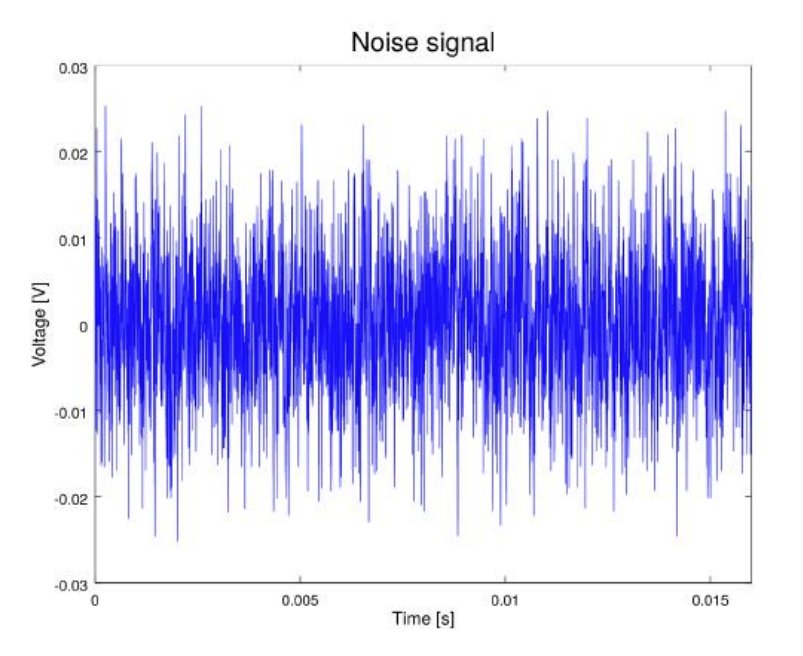
P-17: (poster; international reach) Multiqubit entanglement for public randomness testing vs Google’s quantum supremacy, Quantum 2020 IOP, 2020 (Quantum2020 IOP Conference, October 19-22, 2020, online conference)
W-2: Empirical data in the form of binary sequences laboratory generated as part of quantum processes determined as a result of industrial research as the most optimal for the generation of truly random numbers (shot noise in electronic systems and quantum optics systems)
W-3: Source and statistical data in the scope of the conducted analyzes of the verification of breaking Bell’s inequality to demonstrate the quantum nature of the physical source process based on entanglement correlations
Additional summaries:
More details: goals of the QRNG R&D project. The aim of the project is to explore the most promising technologies of emission and detection of quantum states in quantum measurement regime as the physical processes underlying the efficient truly random (nondeterministic) number generation. The project result will comprise detailed verification of both qualitative and quantitative technical conditions of generated random numbers (in the representation of binary strings), specify the limit parameters of the tested technologies and choose the most optimal ones, on the basis of which a laboratory prototype will be prepared, and subsequently developed to the level of implementation of the integrated prototype of a quantum random number generator, which will be the basis for further development of innovative products and their future market deployments. Truly random sequences of numbers have an essential and critical role in cryptography. As the only cryptographic resource they fully unconditionally guarantee (ie. within the absolute, or otherwise impossible to break regime, regardless of existing technologies and time) encrypted communication security. OTP encryption (One-Time Pad) is the simplest, yet most important cryptographic protocol belonging to the category of classical symmetric cryptography, which was proven formally by C. Shannon in 1948 as absolutely (unconditionally) safe if it is implemented using shared fully random key (nondeterministically random bit strings of length of messages that can be shared before the communication or also unconditionally securely exchanged during the communication only by using quantum cryptography, which also requires true randomness). Research in the field of truly random number generation, are critical mainly for cryptographic applications (other relevant applications are related to scientific modeling, artificial intelligence, video games and lottery gaming). According to the laws of physics all random number generation processes based on the classical macroscopic effects (ie. phenomena governed by the laws of classical physics) are inherently deterministic, that is, in fact, constitute only the source of pseudo-random numbers. While for many applications such sources are sufficient, in the case of security level of cryptosystems they constitute a serious security hole. Within the information security industry, the National Encryptor (representing the name of the project of the consortium of the Wasko SA company and the Military University of Technology completed three years ago within a funding from the Ministry of Internal Affairs and Administration) became famous along with numerous media publications. The device (whose prototype has been built and commercial and special mass production deployments are currently being sought) has been acclaimed by media as a success greater than the Polish contribution to breaking the Enigma during World War II, and as the new non-breakable encryption device, receiving a series of awards in various inventiveness and innovation competitions. Implementation of the device is based on the elliptic curve cryptography (ECC) paradigm, i.e. a type of asymmetric cryptography, whose security fully conditioned by the theory of computational complexity. In the case of elliptic curves, the difficult problem, i.e. a problem with computational complexity growing exponentially with input length (e.g. the length of an encryption key), is the problem of finding the discrete logarithm. Without belittling the deserved media publicity of valuable national cryptographic initiatives and contribution of the discussed project to initiatives towards emphasizing the significance of cryptography, it should be noted that this device does not offer any unconditional level of security at all, and its media “non-breakability” is just a myth resulting from incomplete presentation of the issue (partly also more or less intended by its creators, indicating that non-breakability stems from the fact that in order to crack the cypher with specific parameters one would need to use the whole computing power available to the mankind for a period of the age of the universe, i.e. 14 billion years). This however lacks a very important clarification that such situation would limited by a number of critical assumptions: firstly that no efficient classical algorithm for calculating the discrete logarithm will be invented (many spectacular breakthroughs tend to occur in algorithmics), and secondly, that no universal (scalable) quantum computer will be implemented (for which Peter Shor already in 1994, gave an efficient, i.e. with polynomial computational complexity, algorithm for finding the discrete logarithm based on quantum Fourier transform, which is also related to an efficient solution to the prime factorization problem – that also constitutes a common schema for computationally conditioned asymmetric cryptography, e.g. within an RSA cipher very commonly used in the Internet – or even broader class of problems of finding an order in modular algebra or finding the hidden subgroup within the group theory – according to generalizations by Alexei Kitaev, 1995). In accordance with the principle of Kerckhoffs the safety of each cipher is fully dependent on a key – in asymmetric cryptography systems, which include the National Encryptor, where the key is protected by complexity of ECC problem, which can be broken thanks to algorithmic or technological progress (quantum computer). A different situation applies to OTP cipher and quantum key distribution QKD that are unconditionally secure, and they are based on true, non-deterministic randomness. From the strategic perspective of the European security, it is important that research on the effective generation of random sequences were implemented in the EU. More details: QRNG market perspectives. The concept of QRNG attack – an attack on systems whose security is based on the classical (and therefore deterministic and predictable) random number generators (RNG), takes a very serious overtone in the light of events such as: compromise of PlayStation 3 systems in 2010 and user account data leak due to non-random one-time nonces for digital signatures, discovery of back doors in RSA security systems utilizing Dual_EC_DRBG random generators deliberately promoted by the American NSA agency, compromise of a part of RSA keys in 2012 connected with low quality random seed (initiation vector IV), or as a result of 2013 Snowden reports about NSA activities resulting in public undermining of the safety of integrated hardware random number generators from, among others, Intel and Via, that are widely used in computer systems worldwide. RNG attacks have been successfully used in currently rapidly growing area of Bitcoin electronic currency – in 2013 errors in Java libs for Android have been revealed, which enabled theft of Bitcoin electronic currency from private virtual wallets; also over 750 thousand Bitcoins (with a current value of nearly 200 mln USD) have been stolen by taking advantage of vulnerability arising from predictable randomness of generated markers; in Jan 2015 the Bitstamp service (one of the most popular Bitcoin to USD online exchange services) suspended all operations due to compromise of internal wallets as a result of the RNG attack. Together with the information from the PricewaterhouseCoopers report (PwC 2015) indicating a 41% increase in the number of cyber attacks detected in 2014 as compared to 2013, and a suspected similar increase in undetected attacks, the problem of IT security that is based on RNG becomes a critical problem of strategic nature for both economy and national security. According to the PwC report 2015, the global IT security market is steadily growing and has now reached a 71.1 billion USD budget with 7.9% increase as compared to 2013 (is assumed to exceeded 77 billion USD in 2015). Europe is one of the key areas of this market, which is correlated with strong increase of capital investments in the IT security sector. In the private sector, in companies with turnover greater than $100 million, a gradual increase in budgets allocated to IT sec. is observed. Awareness of the cybercrime risks is growing, probably partly due to the increase of the losses resulting from security breaches (a leap from 34% to 92% is observed in an increase of the losses in various branches of the private sector of the world’s information-based economy). It should be emphasized that large portion of incidents is not reported at all, and that incurred losses are in most cases very difficult to estimate (particularly due to copyrights and intellectual properties). According to the World Bank estimations from 2014, exposure of trade secrets can cost from 749 billion USD to as much as 2.2 trillion USD annually. In the survey conducted in 2014 addressed to managers in the private sector, PwC revealed, that despite the fact that more than half of the respondents estimated increase in risks awareness of up to 39% compared to 2011 (Economic Crime, PwC 2014), large organizations still experienced a drastic increase in the cost of damages caused by cyber attacks by more than 50%. Similarly, Symantec’s report of 2014 informs about a strong upward trend in both the number of computer attacks (in some cases up to 700% compared to 2012) as well as the associated costs of such intrusions. Despite the fact that currently almost every IT service utilizes a number of security measures (auth., validation, certification, encryption), the underlying security of almost all commonly used cryptographic methods is based on random numbers (e.g. generation of keys for encryption systems, or markers for auth. procedures, including OTP, WC, AES, DES, RSA, DH, DSA methods), which are currently at a global scale generated in a manner that enables prediction of their ‘randomness’, allowing for effective RNG attacks that compromise the entire cryptosystem. In the area of information security RNGs are most commonly used for generation of cryptographic parameters, init. vectors IV, one-time markers – so called nonces, codes in PIN/TAN systems, authentication and authorization processes for digital signatures, code in pre-paid systems for mobile telephony, or encryption keys for OTP one-time-key ciphers (inc. encryption of e.g. video transmission – which requires considerable speeds of random sequence generation). A growing number of computer software packages are to a large extent based on the availability of random number sources – in some cases, such packages use random numbers in large amounts, e.g. SSH, SSL, GPG, etc. The truly random numbers also constitute a basis for the unconditional security of quantum cryptography – a forward-looking technology and only possible protection of communication from emerging quantum computers. The global market is showing a demand for stable and flawless technological solutions aimed towards minimizing of the risks resulting from low quality randomness of generated numbers, while maintaining the cost-effectiveness and efficiency parameters (speed). The basic solution proposed by a number of companies (including Intel, IBM, etc.) are so called hardware RNGs (HWRNG hardware random number generator) meant to replace the pseudo-RNG. These hardware solutions are, however, still based on fully deterministic electronic systems governed by the laws of classical physics, which, in the face of the unconditional security paradigm, does not provide relevant guarantees and still leaves a critical hole in the security of a whole system. Only generators based on quantum physical processes, with maximum theoretically attainable entropy for each bit position (equal to 1), can provide true randomness of generated sequences. There are currently only 2 products commercialized worldwide, whose concepts are based on non-determinism of quantum mechanics and several circuits in prototype phase and pre-commercialization, and several more systems in prototype and pre-commercialization phases. The proposed Polish solution within this fundamental area of security may constitute a key aspect of the national security, especially in the light of questionable activities of NSA or eastern states. In addition, truly RNG will find (less critical but still important) application in the area of numerical modeling and simulation (e.g. Monte-Carlo methods, frequently used for economic simulations in the financial sector), in the field of AI, in video games, gambling and lotteries, as well as research and statistical analysis methods, where true randomness of data or group selection is essential. This is a secondary area of the project’s implementation potential, which the applicant plans to implement in the area of security, but also plays an important complementary role More details: QRNG economical briefing The main target group for advanced security systems, for which a quantum generator will be an important component, is the financial sector in the context of online banking. The key element for securing such transactions are hardware generators of PIN/TAN tokens based random number generators. SecurEnvoy shows that hardware tokens still constitute a better protection than transferring tokens through. In Poland, according to the Special Eurobarometer 423. Cyber Security Report – Fieldwork of 10.2014 – 57% of the population uses online banking, and in Europe on average 54%. 85% of all respondents (in Poland and EU) indicate a significant risk of becoming a cybercrime victim. The primary security measure for online banking transactions are tokens based on truly random numbers (that can be obtained only in a quant. way) for the PIN/TAN, which will eliminate the possibility of performing an RNG attack. Improving the online banking security is an important element of financial expenditures in the banking sector, which, according to PricewaterhouseCoopers increase its IT security spendings by as much as $2 bln over 2 years. In 2014, more than 750 entities from the financial sector jointly spent $4.1 bln on IT security, which indicates a large financial potential of this area. The market that uses the private key (whose formation is based on random number generation) paradigm for cloud data storage services in distributed systems is also developing very dynamically. Centaur Partners predict an increase of the cloud services market from $13.5 bln in 2011, to $32.8 bln in 2016 and yet to $200 bln in 2018 (Infonetics Research). The use of TRNG truly random numbers generators is essential for the safety of symmetric crypto. algorithms frequently used to secure data within the services of cloud architecture. Providers of these services will constitute another target group of the project results (also the area of asymmetric crypto. traditionally disseminated in the Internet in e.g. RSA, DSA, DH ciphers random numbers are critical for gen. of a key pair and provide the security of relevant cryptosys.). Almost every paradigm of classical crypto. is based, in its assumptions, on ideally random crypto. init. vector/seeds – ranging from the symmetrical methods (including OPT, WC, AES, DES) to asymm. methods (including RSA, Diffie-Hellman, DSA). IT security market estimates range from $71 bln in 2014 to more than $155 bln in 2019. Increase in IT security spendings in 2015 is to be the order of 8.2% to the value of 76.9 bln in 2015 (Gartner, Inc.). Investment in next-generation IT security solutions are expected to reach between $15 bln to $20 bln over the next three years. It is estimated (FBR Capital Markets), that in 2015 an increase in investments in next-generation security solutions IT is to be the order of 20%. To ensure high cyber-security level, transition to the unconditionally secure crypto. systems paradigm is necessary – and the production of such is only possible with possession of the sources of truly random numbers, that is – based solely on the quantum laws. In the area of OTP cipher applications, in case of streaming encryption of significant intensity (e.g. encryption of a video transmission), in addition to the req. of quantumness of the gen. method, also a proper generation rate is essential, as well as the cost effectiveness of the solution. In the Global Cybersecurity Status Report survey of 2015 conducted among 3439 entities from the area of IT area from around the world, the question of whether they feel that their organization will be the target of a cyber attack in 2015, was answered ‘yes’ by 46% of respondents (30% were not sure). When asked whether they considered the cyber attack as one of three most serious threats to their organization, up to 83% answered ‘yes’ (5% were not sure). Only 38% of all respondents felt that their organization is prepared to repel sophisticated attacks. This means that current security methods are not sufficient and along with increasing risk awareness, the market demand for unconditionally secure solutions will be growing. Another target group can be identified in one of currently most dynamically developing areas of electronic services. The market of the most important e-currency Bitcoin, whose system for virtual wallet generation within the virtual currency exchange services requires the use of fully randomly generated numbers, shows a continuous and very dynamic growth. Since 2011, a significant upward trend is observed in regard to the number of transactions performed in this currency daily (several thousand in 2011, currently more than 100 thousand per day – blockchain.info). The daily Bitcoin trading volume already reached $40-50 mln. Dozens of sites that allow users to buy, store and exchange Bitcoins for the fiat currencies, service a growing number of users. Each of these services is exposed to a possible RNG-type attack due to not employing a truly random number generators, and constitutes a potential deployment area of the product, especially due to loud media reports about further possible attacks on virtual wallets (e.g. suspension of Bitstamp operation in January 2015). It is also necessary to consider the growing market of quantum crypto. security – the value of this new market is estimated at $842 mln in 2015 according to GIA and Frost & Sullivan international research report. The recipients of services in the field of quantum crypto. are both public and private sector entities, whose activities are related to the use of modern IT technologies, and for which the safety of the processed data is of a particular importance, which implies the need for advanced solutions in the area of security. Quantum crypto. (being the only protection of communication against emerging quantum computers) needs to be based on quantum randomness to provide unconditionally secure cryptosys. In addition to the target groups from the area of IT security, one can identify potential recipients of the project in the group of research inst. conducting numerical simulations, in particular employing the Monte-Carlo the methods, as well as developing artificial intelligence. In case of these methods, it is crucial to ensure the true randomness of consecutive samples (with gen. speed and cost-effectiveness), which is not possible with the current software or hardware RNGs, due to their classical nature. This market includes, among others, IT corporate sector, analysis, financial, computer graphics, engineering, and basic research sector. Also entities from the video games, gambling and lotteries sectors may constitute a potential recipients of the project results. In 2015 the size of the computer games market reached $81.5 bln, including $280 mln in Poland (Global Games Market Report), while the online casinos market – a value of $41.4 bln (both markets experience a steady upward trend for more than 10 years) – Statista.com. More details: QRNG technology international competition Random number generators market is now dominated by the classical generators, both software and hardware. Companies producing components of computer systems (IBM, Intel, HP, Lenovo, Apple and others) integrate dedicated electronics as a number generators (RNG). However, the current reports of succesive compromises of cryptographic systems using RNG attacks indicate that the current market requires a qualitative change in a broad scale mainly in key areas for security. One can indicate a number of companies producing external random number generators inf the form of computer peripheral devices (for external USB interfaces, serial ports and internal connectors such as PCI, PCMCIA, etc.), offering access to a stream of numbers generated in small electronic circuits, characterized however by full determinism of operation (due to the operating principle based on the laws of classical physics) influencing the safety of the proposed solutions. Such classic RNG products include:- – SGCL-1 MB – a domestic product of the Military Institute of Communications – hardware RNG. generation rate of the order of 8 Mbps, USB link. Product price starts from 2 thousand PLN.
- – TL200 from TectroLabs, USA – hardware RNG that uses random noise generated by two independent stable sources based on the Zener diodes in the biased states. General-purpose device with a USB interface and USB-powered, generates a stream of random bits at speeds up to 2 Mbps. Integrated raw processing algorithms to be based on the SHA. The unit price of $299.
- – Araneus Alea II from Araneus Information Systems Oy, Finland – hardware RNG using the semiconductor in biased states generating broadband white noise processed from several samples by the microprocessor into output bits. USB device powered by USB port, generates a stream of random bits at a rate of 100kbps. The unit price of 219 EUR.
- – GRANG from LETech Co., Ltd., Japan – hardware RNG using thermal noise (white noise) from the resistor, generating pulse trains whose registration times are measured and converted into numerical values. The company offers a range of solutions from server generating 50-150 Mbps through 50 Mbps PCI cards, 7 and 2 Mbps chips, 50 Mbps SATA module, 10 Mbps USB devices and finally the 300 kbps IC chip Grange-TEG. 550 Mbps PCI module is also offered. Prices for standard 2 Mbps systems range from 400 USD.
- – TrueRNG from ibld.it, USA – hardware RNG based on classical properties of semiconductor electronics. A device with USB interface powered by the USB port, generates a stream of random bits at a speed of 350 kbps. Compatible with Beaglebone environments, Raspberry PI, UDOO. The unit price of $49.95.
- – SG100 EVO-USB and USB-R230 from Protego Information AB, Sweden – hardware RNG that uses the semiconductor and classical thermodynamic noise (Johnson noise) to generate random bits. A device with a USB or serial interface. Generating rate of 8 kbps to 2 Mbps. Price 249 EUR (SG100 EVO-USB) and EUR 1195 (R230-USB).
- – Also solutions of integrated circuits manufactured by world leaders in chip technology are available, for example Xilinx – creators of the FPGA architecture. One of the products Xilinx is the CLP-800 Smart True Random Number Generator using system with source of the classical noise that generates a stream of random bits. The manufacturer claims that the device can operate at generation rates of the order of 1 Mbps. It is compatible with FIPS 140-2 and 140-3.
- – Quantis from idQuantique company, Switzerland – a quantum RNG based on the laws of quantum optics using a beam-splitting component. Offered models have various connection interfaces – USB, PCI, PCIexpress. Depending on the type, the generators provide generation rate of 4 Mbps for USB and up to 16 Mbps for PCI and PCIe with <1% random bits resulting from thermal noise. Autoverification, entropy consistent with the NIST (above ~1-2^64). Prices depending on the model: Quantis-PCIe-16M Card – 2990 EUR Quantis-PCIe-4M Card – 1550 EUR Quantis-USB-4M module – EUR 1150, Quantis-PCI-1 Card – 1350 EUR Quantis-PCI 4 Card – 2590 EUR.
- – PQ4000KU and PQ32MU from ComScire, USA – quantum RNG using shot noise associated with the gate tunneling and threshold leakages on semiconductor joints. The PQ4000KU device offers generation rate of about 4 Mbps, USB connection with power supply; PQ32MU model offers generation rates of 32 Mbps, also USB interface. Autoverification, entropy above ~ 1-2^64. The characteristics claim autocorrelations fewer than 1 per trillion. Product prices: ComScire PQ4000KU – 895 USD, ComScire PQ32MU – 1495 USD.
- – QuRNG 50 from qutools GmbH, Germany – quantum RNG based on quantum detection of optical LED emission (time offsets of photon counts). The device is claimed to eventually provide a generation rate of 50 Mbps. USB connection, the generated data stream does not require processing. Autoverification, entropy above ~ 1-2 ^ 64. No commercial offer.
- – PQRNG 150 from PicoQuant, Germany – a quantum RNG based on ecxamination of the timing of nondeterministically behaving single photons. The manufacturer claims an objective to reach generation rates of 150 Mbps via the USB interface. Autoveriication, entropy above ~ 1-2 ^ 64. No commercial offer.
- – QStrem from QuintessenceLabs, Australia – currently declared as the world’s fastest random number generating device in the manner claimed by the manufacturer as quantum. Operation based on the use of quantum photon vacuum states as a source of random quantum noise. The rate of 1 Gbps, in the homogeneous conditional entropy regime (8 Gbps for raw stream). Autoverification, entropy above ~ 1-2 ^ 64. PCI interface. No commercial offer.
- – MPD QRN from Micro Photon Devices, Italy – a quantum RNG based on statistical distributions of quantum detection of electron-hole pairs excitation in semiconductor. Declared target rates of 16, 32, 64 and 128 Mbps. Autoverification, entropy 1/bit above ~1-2^64. USB interface. No commercial offer.
WROCŁAW UNIVERSITY OF SCIENCE AND TECHNOLOGY QRNG RESEARCH COOPERATION
For more details on the research carried out by the WUST Department of Quantum Technologies and the National Quantum Technologies Laboratory, refer to: https://seqre.net/jurand-project-results-wust. This section disseminates results of the project “JURAND – National Quantum Random Number Generator” implemented accordingly with the EU co-funding agreement no. POIR.01.01.01-00-0173/15 with the Polish National Center for Research and Development.
This section disseminates results of the project “JURAND – National Quantum Random Number Generator” implemented accordingly with the EU co-funding agreement no. POIR.01.01.01-00-0173/15 with the Polish National Center for Research and Development.
THE OBJECTIVE OF THE JURAND R&D PROJECT
The project’s objective is in development of national QRNGs (Quantum Random Number Generators) as critical components for assuring information-theoretic level of communication security in quantum cryptography, as part of the commercialization program towards national quantum cryptography QKD (Quantum Key Distribution) systems.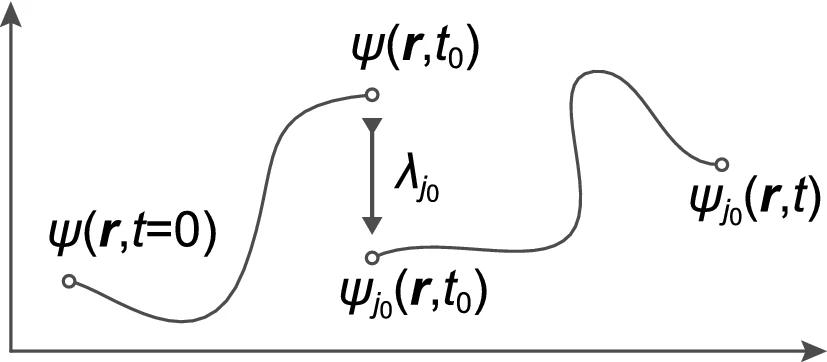 The Von Neumann projection scheme: the quantum state at the moment of measuring of the observable A collapses to a randomly selected eigenfunction of this observable, ψ and the measurement result is a value of a corresponding eigenvalue λ (the real number). The result is hence completely random and the measurement destroys the state Ψ, which ’remembered’ its initial conditions and the system has no further memory on this initial state. The subsequent evolution no longer remembers initial state and begins with a completely randomly selected eigenfuncion of the observable. Quantum measurement is therefore referred to as the wave function (representing state) collapse, a fundamentally nondeterministic process that is the only source of true randomness.
The Von Neumann projection scheme: the quantum state at the moment of measuring of the observable A collapses to a randomly selected eigenfunction of this observable, ψ and the measurement result is a value of a corresponding eigenvalue λ (the real number). The result is hence completely random and the measurement destroys the state Ψ, which ’remembered’ its initial conditions and the system has no further memory on this initial state. The subsequent evolution no longer remembers initial state and begins with a completely randomly selected eigenfuncion of the observable. Quantum measurement is therefore referred to as the wave function (representing state) collapse, a fundamentally nondeterministic process that is the only source of true randomness.
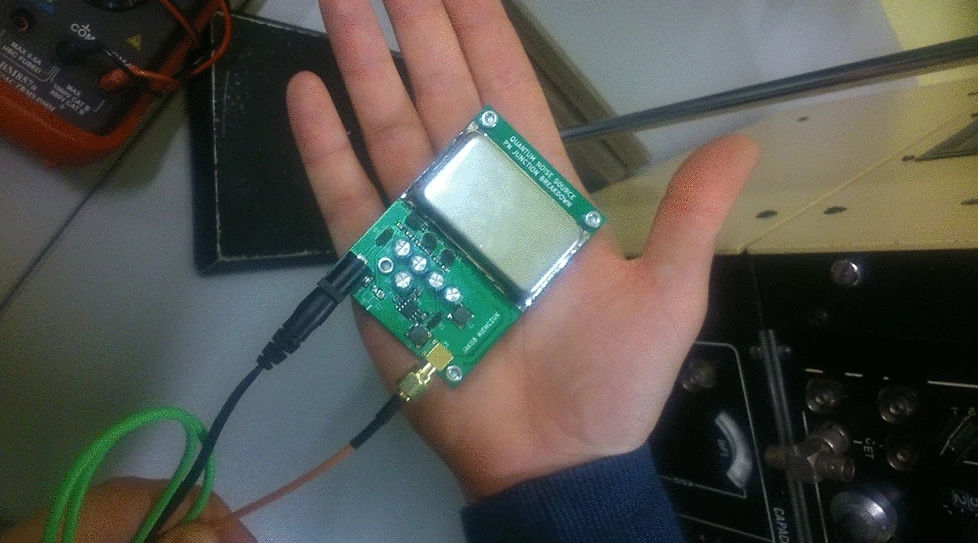 JUR01 quantum random number generator prototype based on the quantum shot noise.
JUR01 quantum random number generator prototype based on the quantum shot noise.
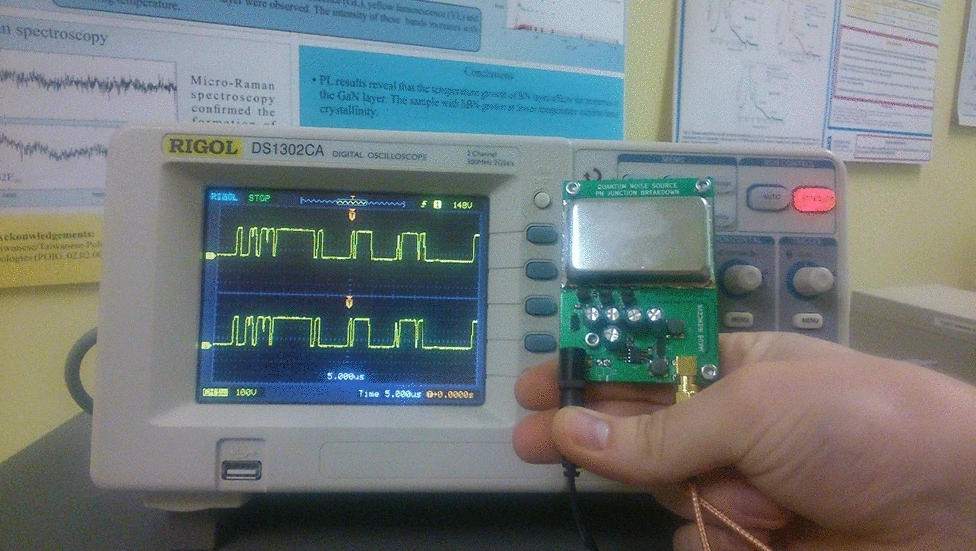 JUR01 QRNG generator performance 4Mb/s of random binary code (on the right panel visible generated random binary signal on the oscilloscope screen).
JUR01 QRNG generator performance 4Mb/s of random binary code (on the right panel visible generated random binary signal on the oscilloscope screen).
 JUR02 quantum random number generator with technical improvements.
JUR02 quantum random number generator with technical improvements.
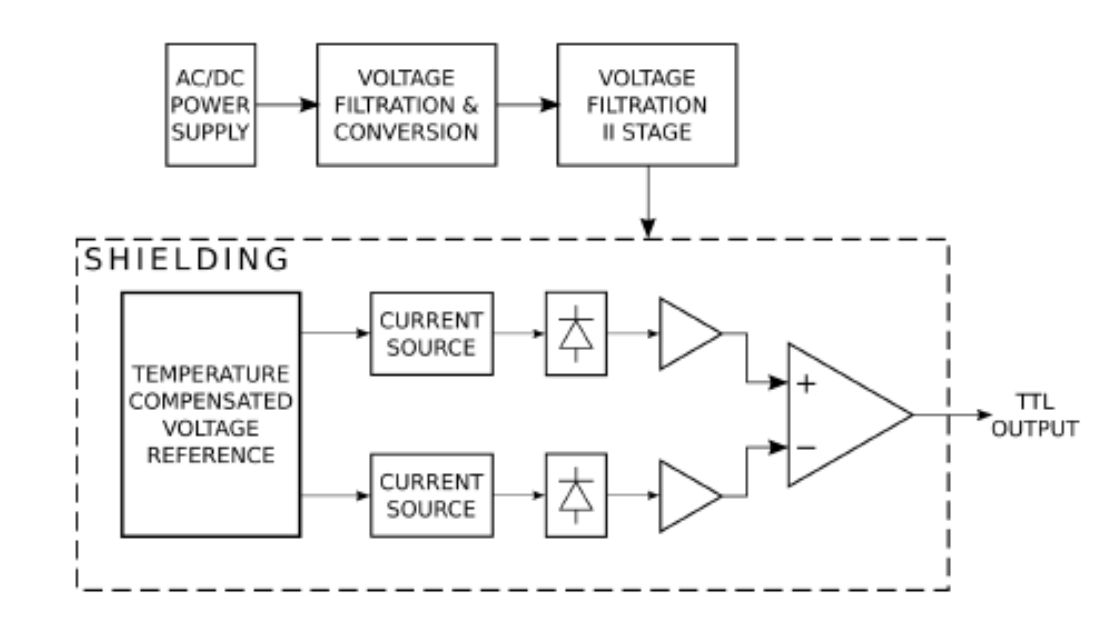
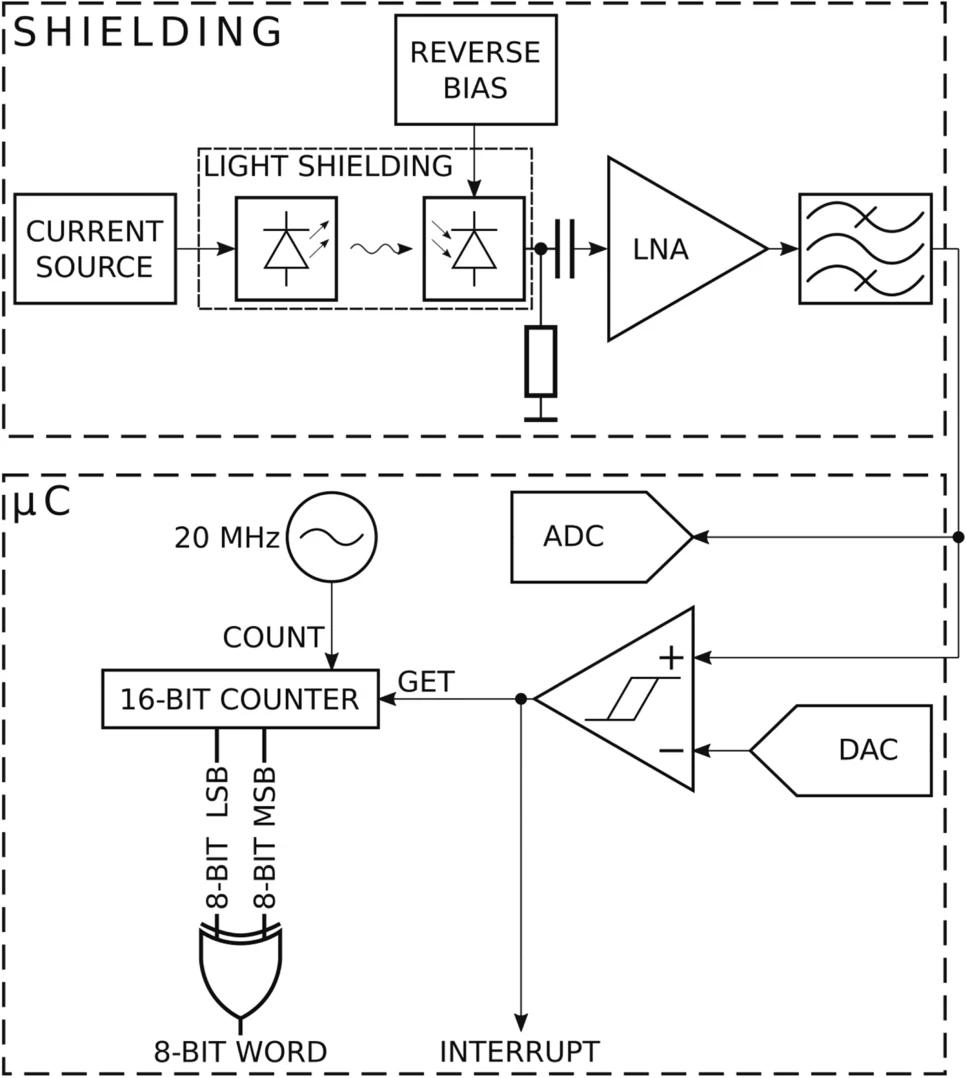 Simplified block scheme of the JUR02 quantum random numbers generator.
Simplified block scheme of the JUR02 quantum random numbers generator.
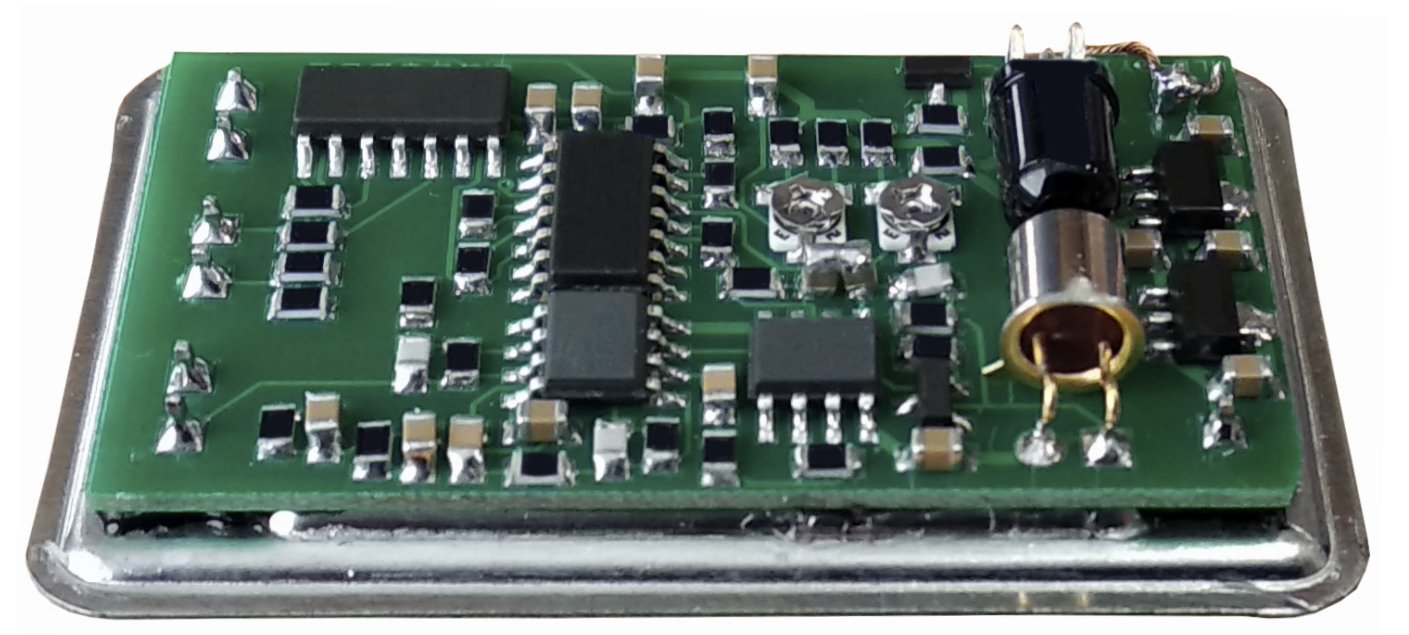 Inner structure of the JUR02 quantum random numbers generator source component.
Inner structure of the JUR02 quantum random numbers generator source component.
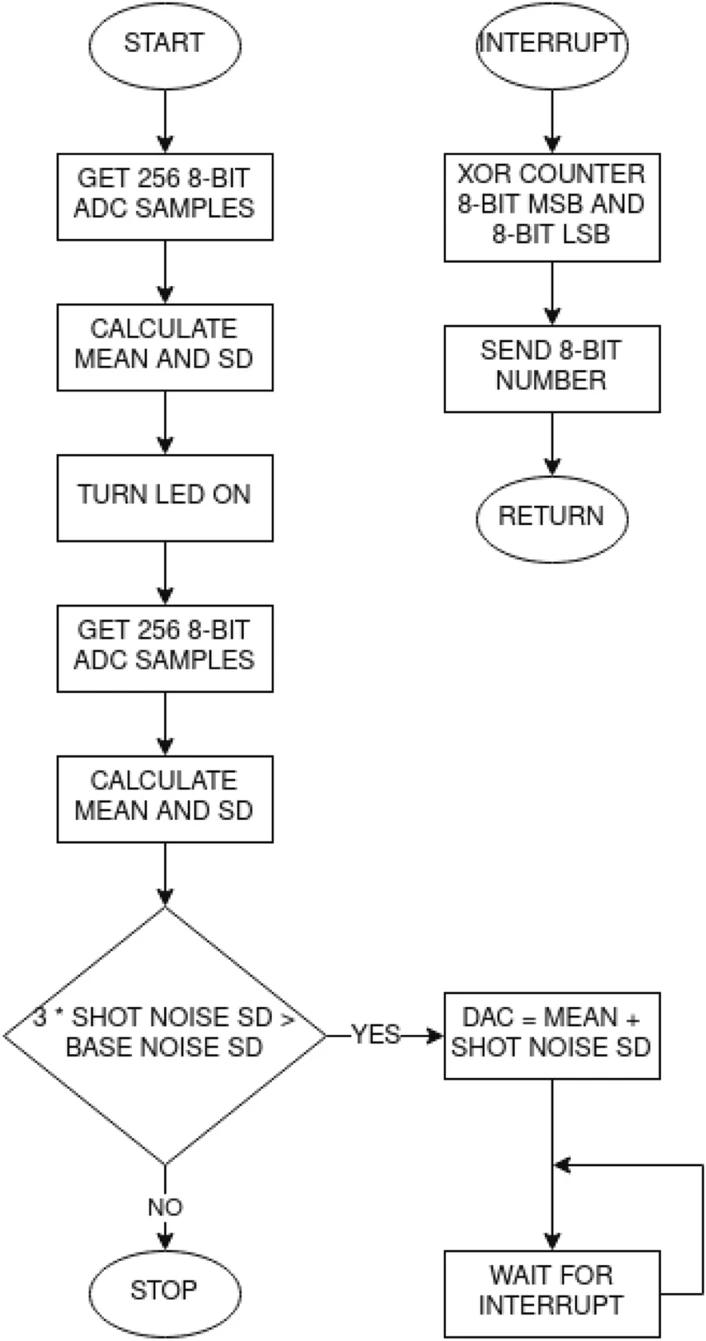 The scheme of the algorithm for automatic starting and calibration sequence and generating of random bit sequence implemented in JUR02 QRNG.
The scheme of the algorithm for automatic starting and calibration sequence and generating of random bit sequence implemented in JUR02 QRNG.
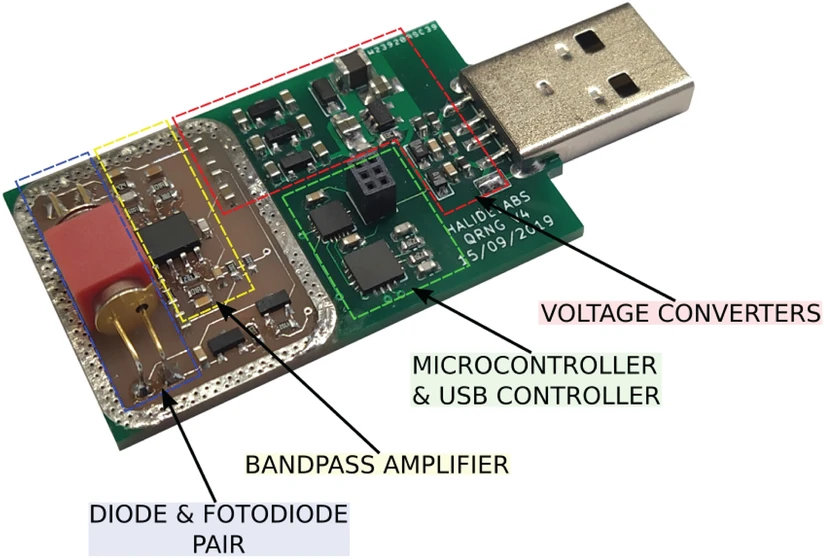 JUR03 shot noise quantum random number generator after significant miniaturization configured with a conventional USB controller (it passed all NIST/Dieharder tests without the bias reduction, at the speed of entropy creation of 1 Mb/s).
JUR03 shot noise quantum random number generator after significant miniaturization configured with a conventional USB controller (it passed all NIST/Dieharder tests without the bias reduction, at the speed of entropy creation of 1 Mb/s).
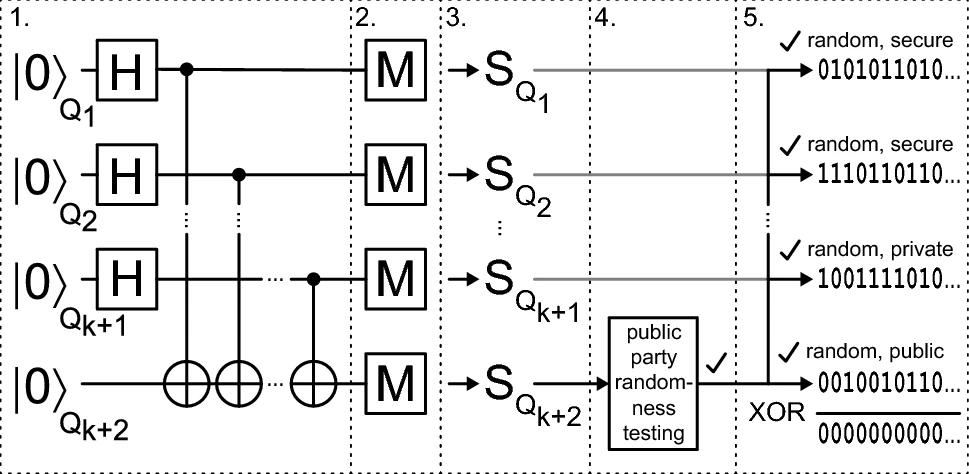 Protocol of the multiqubit, entanglement based, cryptographically secure QRNG with public randomness verification. More details at: https://www.nature.com/articles/s41598-019-56706-2
Protocol of the multiqubit, entanglement based, cryptographically secure QRNG with public randomness verification. More details at: https://www.nature.com/articles/s41598-019-56706-2
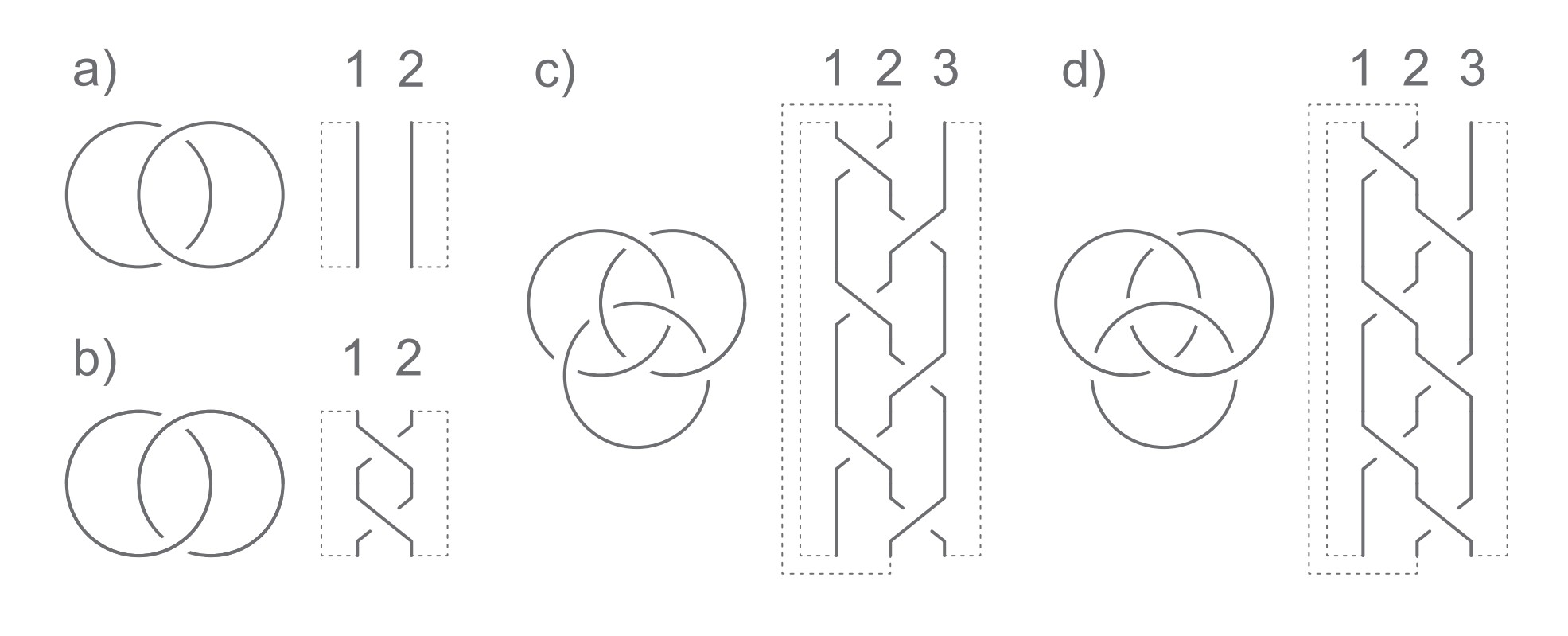 A simple topological model corresponding to inequivalence in terms of topology of the basic quantum entanglement types for two-dimensional quantum systems (qubits). As elements of the braid group are in fact closed loops, the gapped lines were added for clarity.
A simple topological model corresponding to inequivalence in terms of topology of the basic quantum entanglement types for two-dimensional quantum systems (qubits). As elements of the braid group are in fact closed loops, the gapped lines were added for clarity.
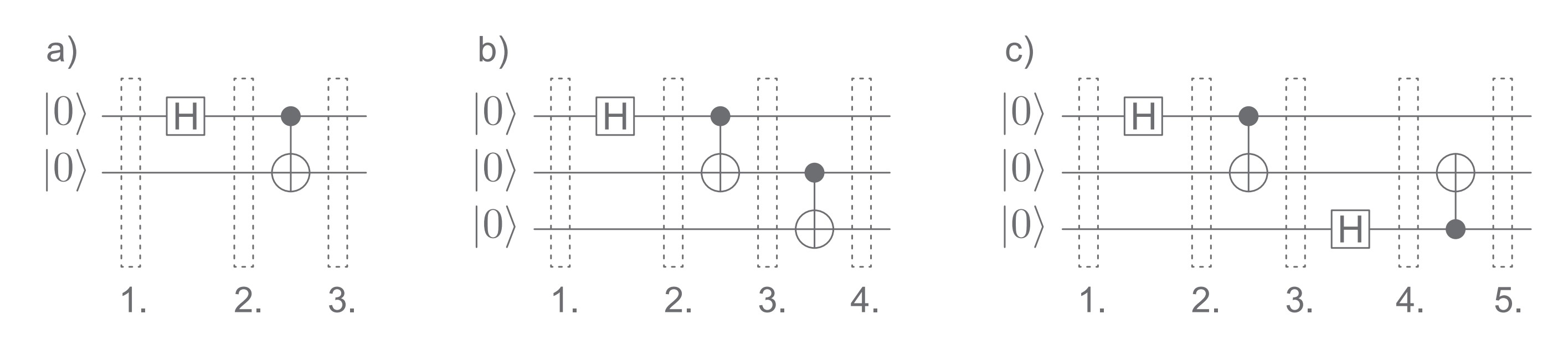 Exemplary basic quantum circuits schemas depicting topologically inequivalent entanglement types generation. Gapped regions depicts consecutive steps of quantum circuit evaluation
Exemplary basic quantum circuits schemas depicting topologically inequivalent entanglement types generation. Gapped regions depicts consecutive steps of quantum circuit evaluation
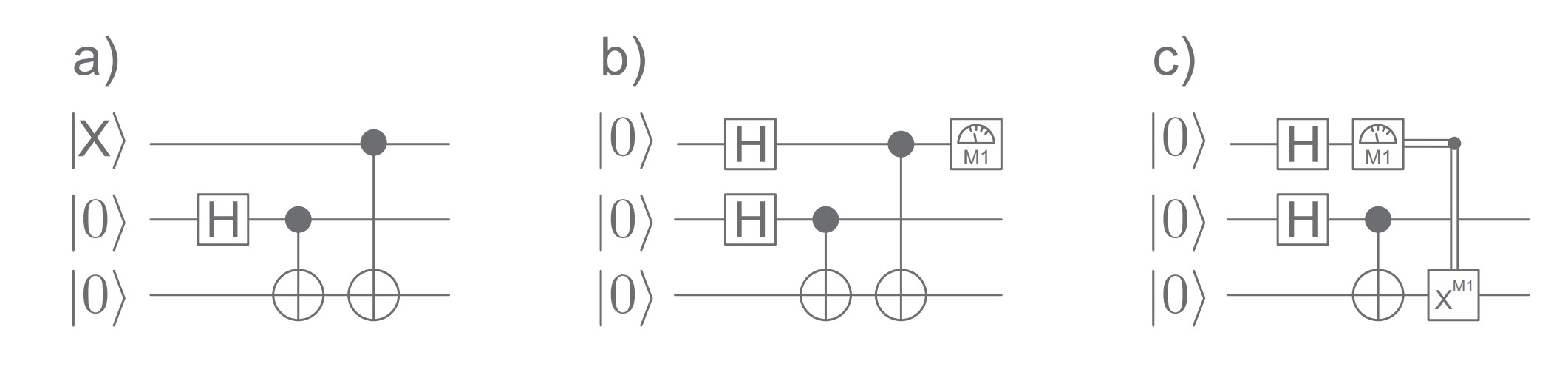 Quantum gate scheme of a random correlation entanglement generator with 2-qubit entanglement state and one auxiliary qubits X. Without (a) or with (b,c) a random selection of 2-qubit entangled state type. Double line represents classical information about the measurement result.
Quantum gate scheme of a random correlation entanglement generator with 2-qubit entanglement state and one auxiliary qubits X. Without (a) or with (b,c) a random selection of 2-qubit entangled state type. Double line represents classical information about the measurement result.
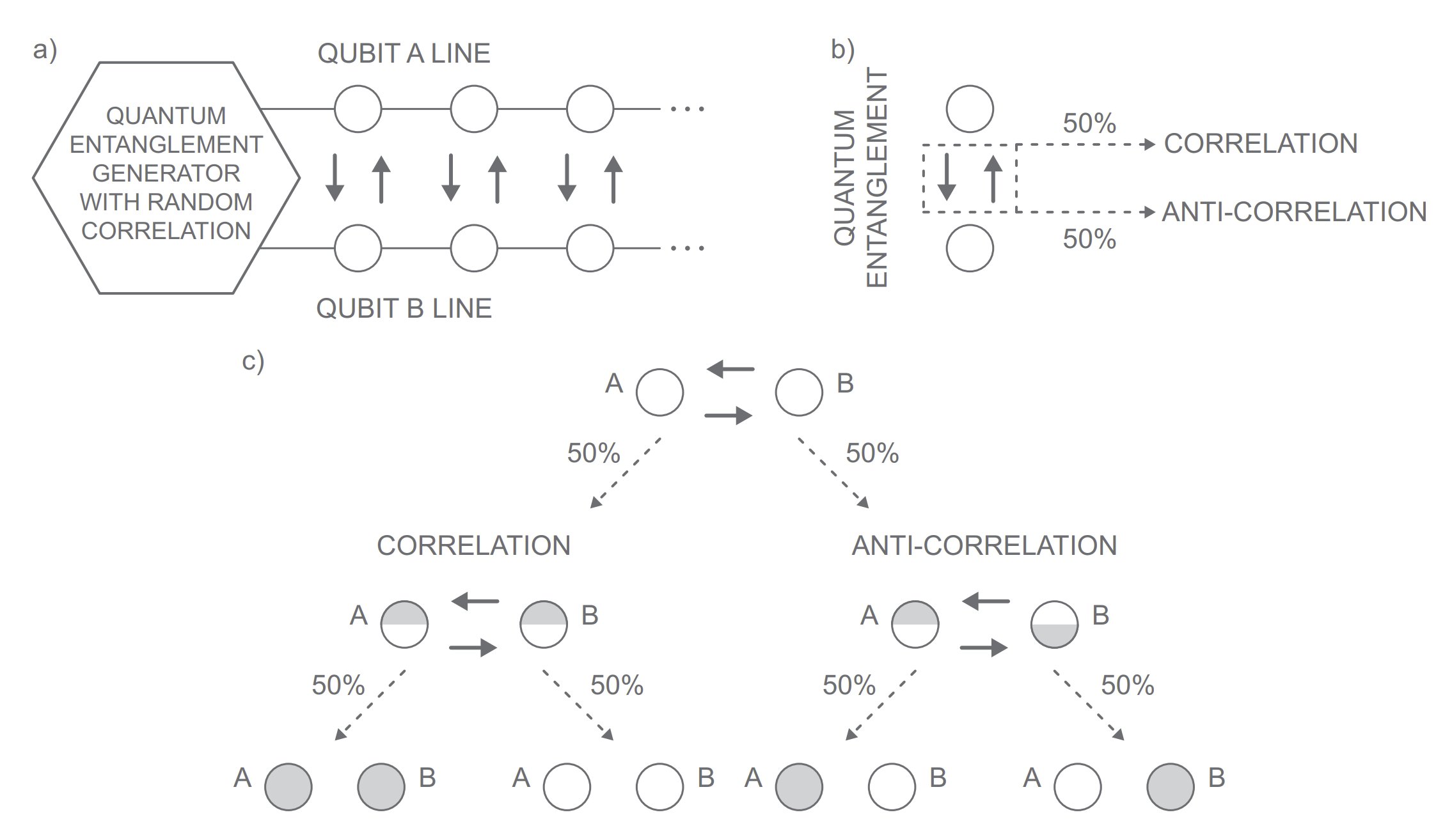 Schematic elements of protocol for quantum random number generator with public proof of randomness: a) generation of random correlations; b) correlation types; c) possible measurement outcomes.
Schematic elements of protocol for quantum random number generator with public proof of randomness: a) generation of random correlations; b) correlation types; c) possible measurement outcomes.
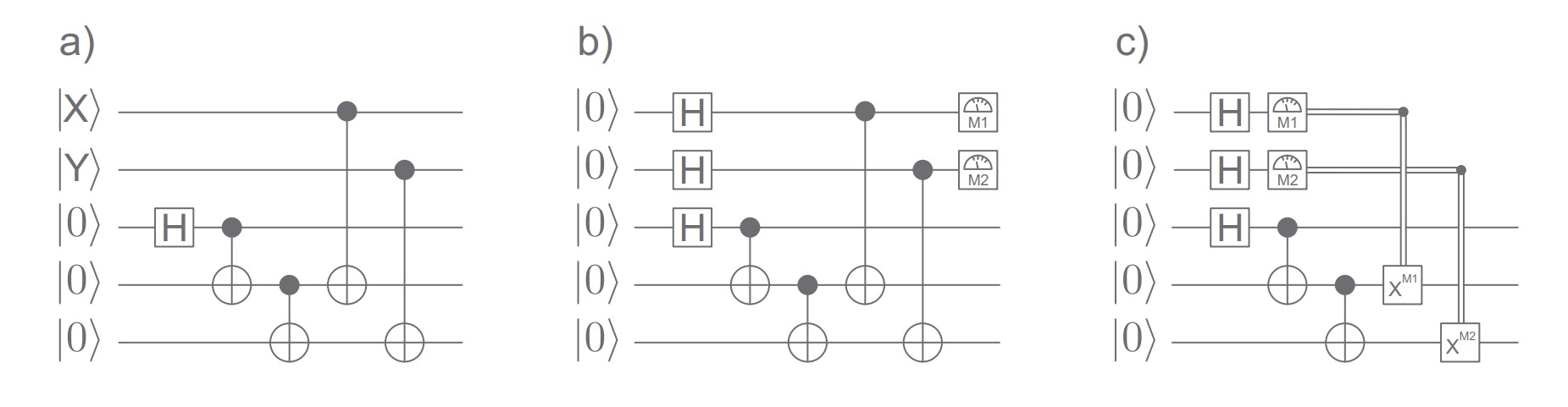 Quantum circuit scheme with gates of a random correlation entanglement generator with 3-qubit entanglement state and two auxiliary qubits X and Y. The generalization of the protocol (increased security of the multiple consent) is attained with the random selection of 3-qubits entangled state type, which is omitted in case (a) and included in cases (b,c). Double line represents classical information about the measurement result.
Quantum circuit scheme with gates of a random correlation entanglement generator with 3-qubit entanglement state and two auxiliary qubits X and Y. The generalization of the protocol (increased security of the multiple consent) is attained with the random selection of 3-qubits entangled state type, which is omitted in case (a) and included in cases (b,c). Double line represents classical information about the measurement result.
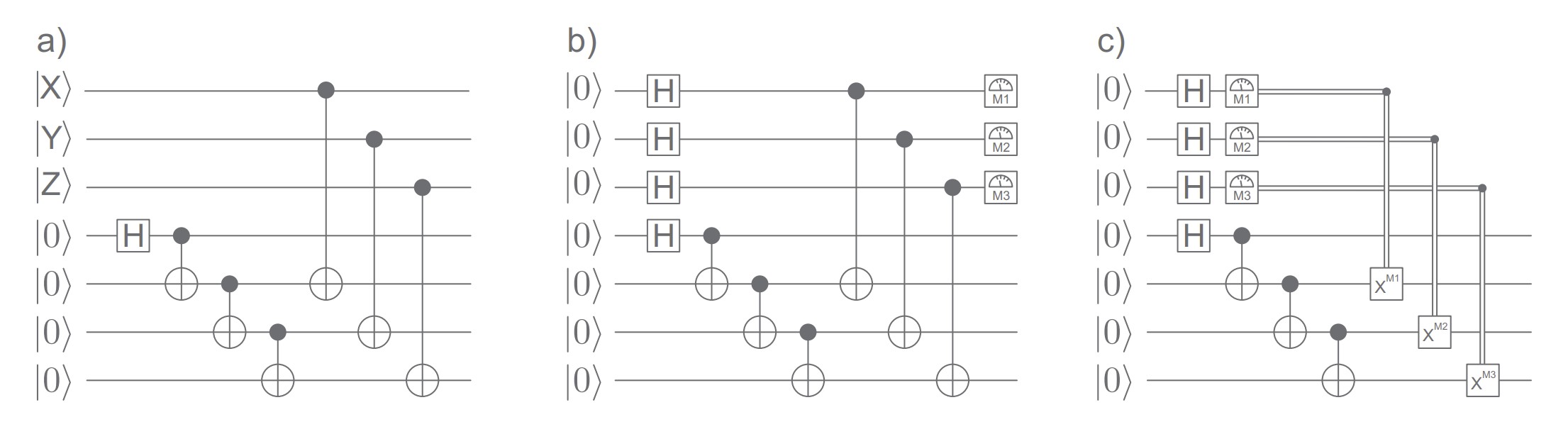 Quantum gate scheme of a random correlation entanglement generator with 4-qubits entanglement state and three auxiliary qubits X, Y and Z. Without (a) and with (b,c) random selection of 4-qubits entangled state type. Double line represents classical information about the measurement result.
Quantum gate scheme of a random correlation entanglement generator with 4-qubits entanglement state and three auxiliary qubits X, Y and Z. Without (a) and with (b,c) random selection of 4-qubits entangled state type. Double line represents classical information about the measurement result.
QRNG THROUGH BELL’S THEOREM
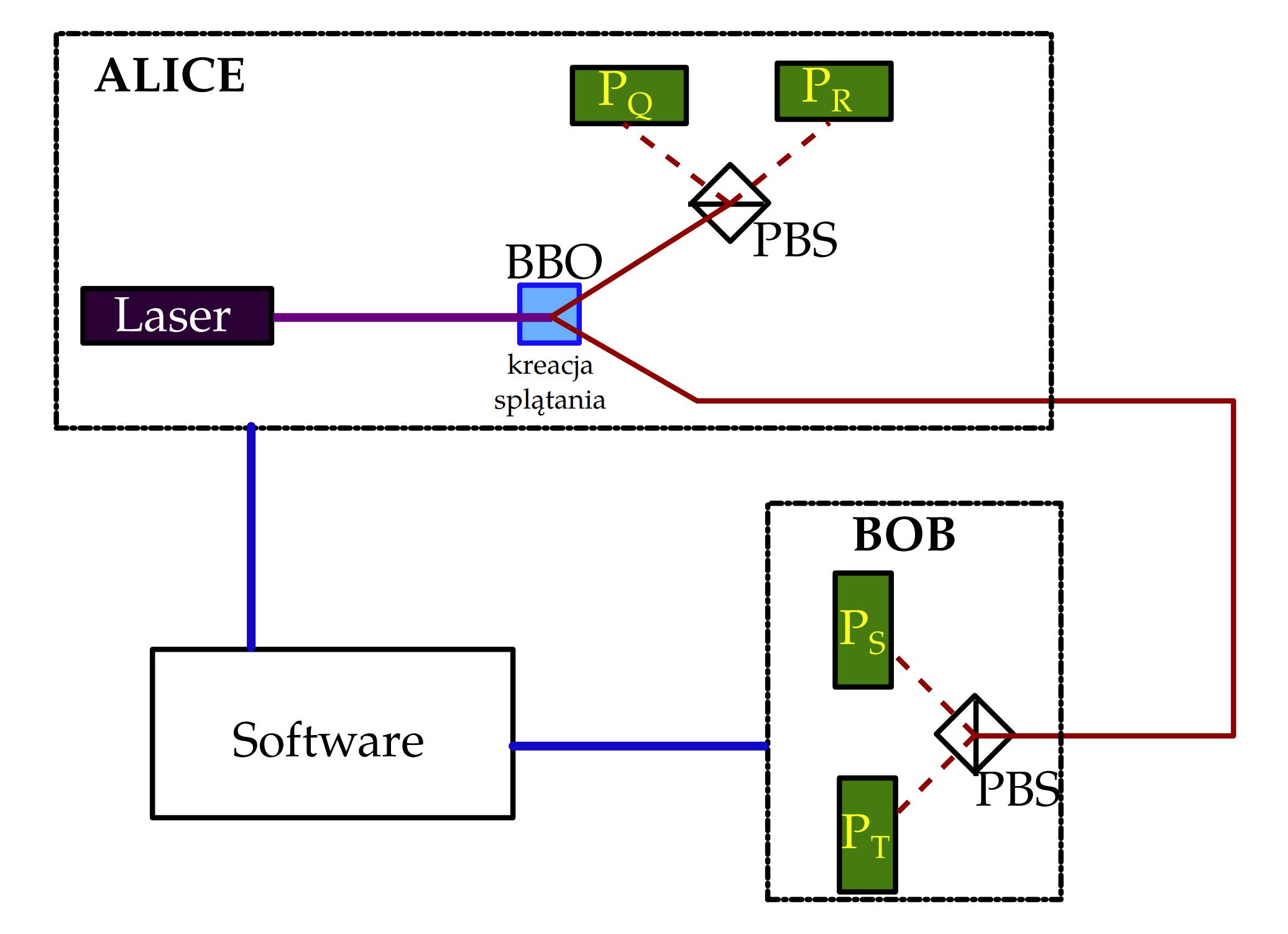 Photon polarization quantum entanglement generation schema in a lab setup for randomness generation.
Photon polarization quantum entanglement generation schema in a lab setup for randomness generation.
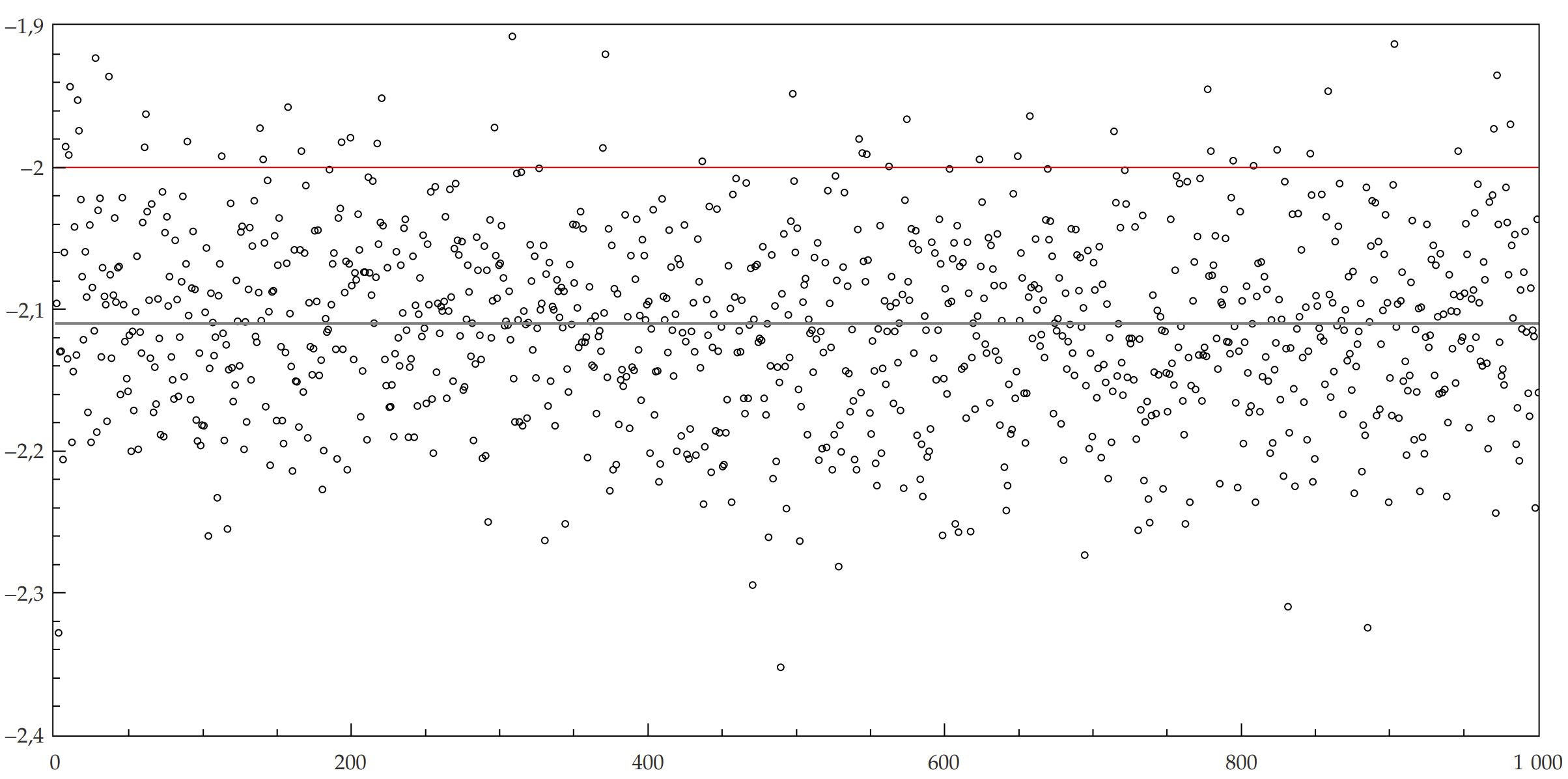 Empirical confirmation of the Bell inequality violation for entanglement based proof of quantum randomness (statistical CHSH expected value exceeding 2).
Empirical confirmation of the Bell inequality violation for entanglement based proof of quantum randomness (statistical CHSH expected value exceeding 2).
EQRNG WITH PUBLIC VERIFICATION
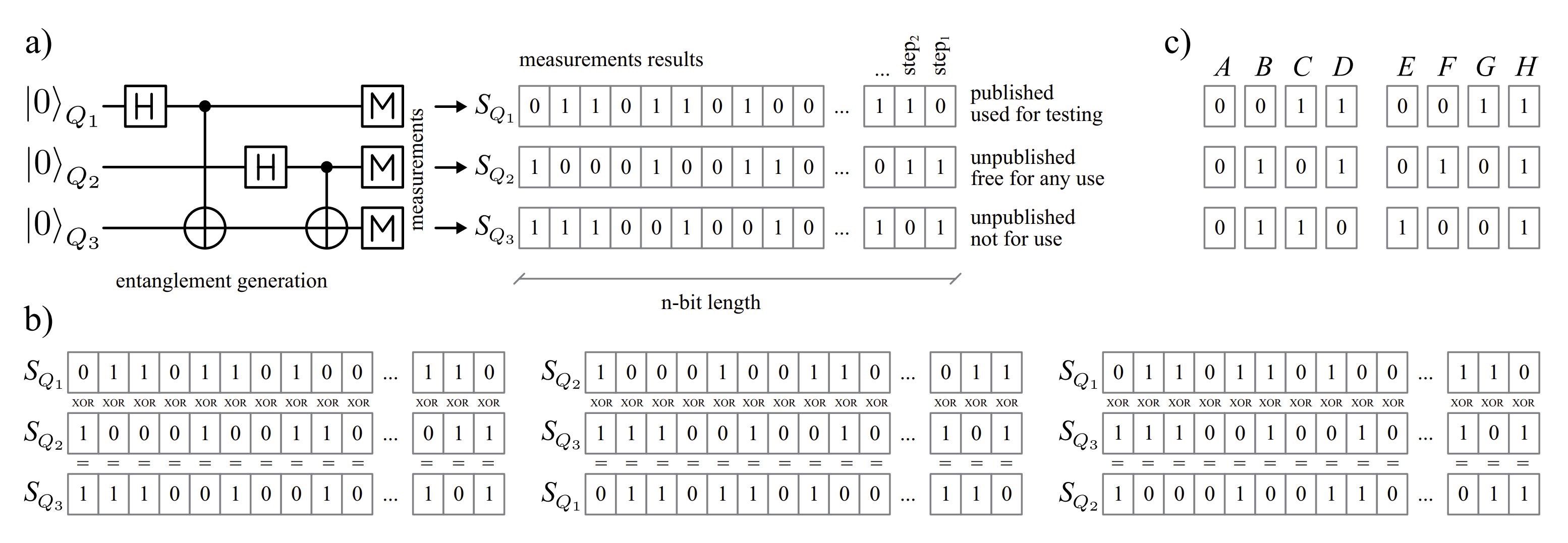 Schemes of QRNG with entanglement for three qubits protocol. (a) Generation, measurements and resultant sequences. (b) So called XOR rule – each pair of bits for any protocol step should give third bit when XOR-ed. (c) A,B,C,D – possible correct measurement results; E,F,G,H – incorrect results indicating bias/error of source or measurement devices.
Schemes of QRNG with entanglement for three qubits protocol. (a) Generation, measurements and resultant sequences. (b) So called XOR rule – each pair of bits for any protocol step should give third bit when XOR-ed. (c) A,B,C,D – possible correct measurement results; E,F,G,H – incorrect results indicating bias/error of source or measurement devices.
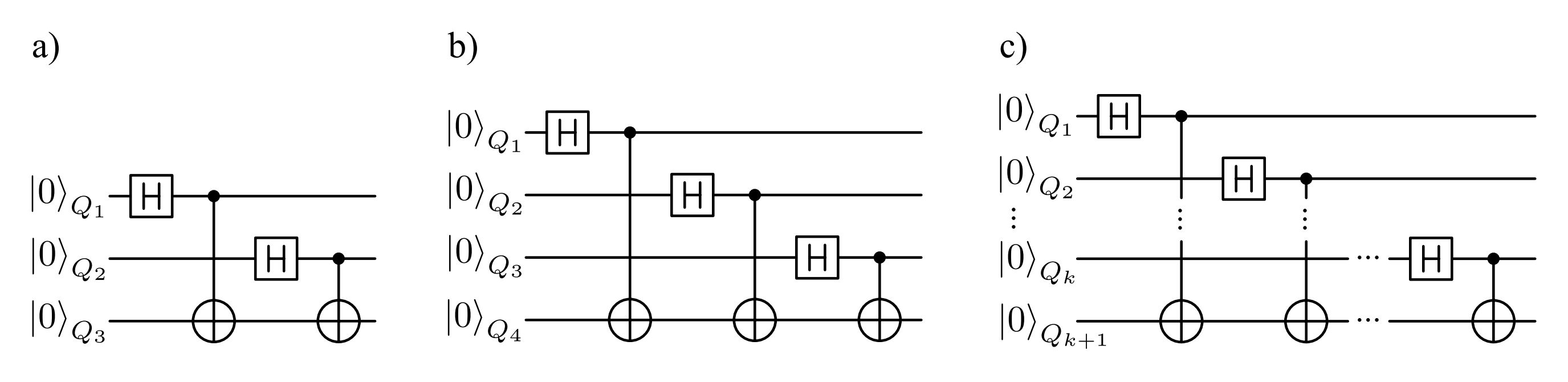 Quantum gate schemes of QRNG with entanglement for (a) three qubits, (b) four qubits, (c) k + 1 qubits.
Quantum gate schemes of QRNG with entanglement for (a) three qubits, (b) four qubits, (c) k + 1 qubits.
EQRNG CONFERENCE PRESENTATIONS

QUANTUM SHOT NOISE QRNG
 Block schema of the JUR01 QRNG system.
Block schema of the JUR01 QRNG system.
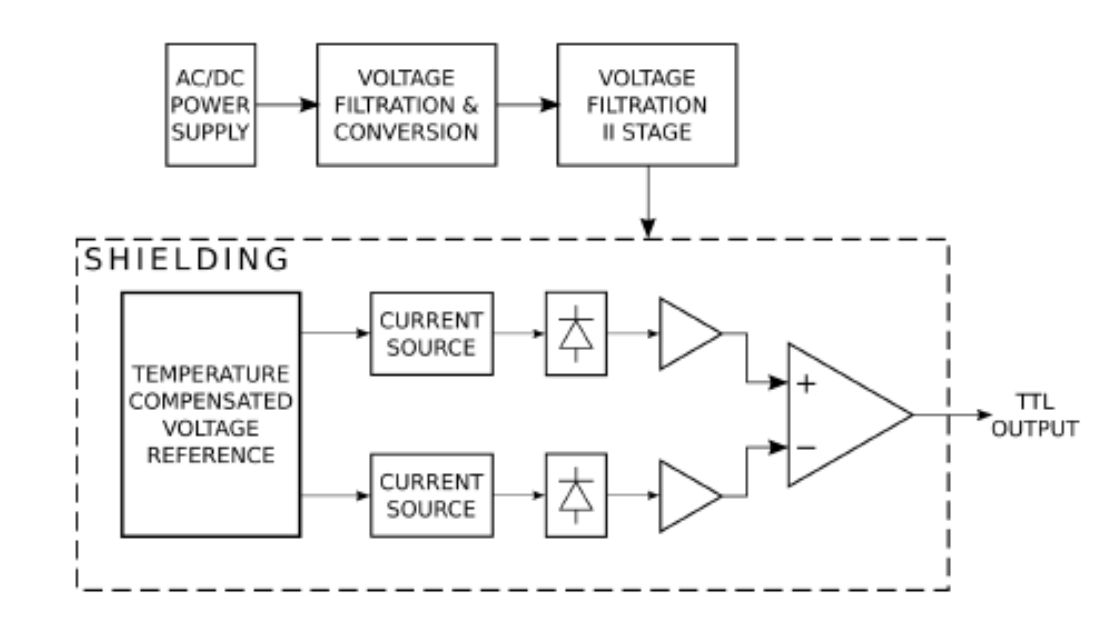
 Enhanced noise signal from one of the shot noise sources used by the JUR01 QRNG system. Sampling at 400ns (RIGOL DS1054).
Enhanced noise signal from one of the shot noise sources used by the JUR01 QRNG system. Sampling at 400ns (RIGOL DS1054).
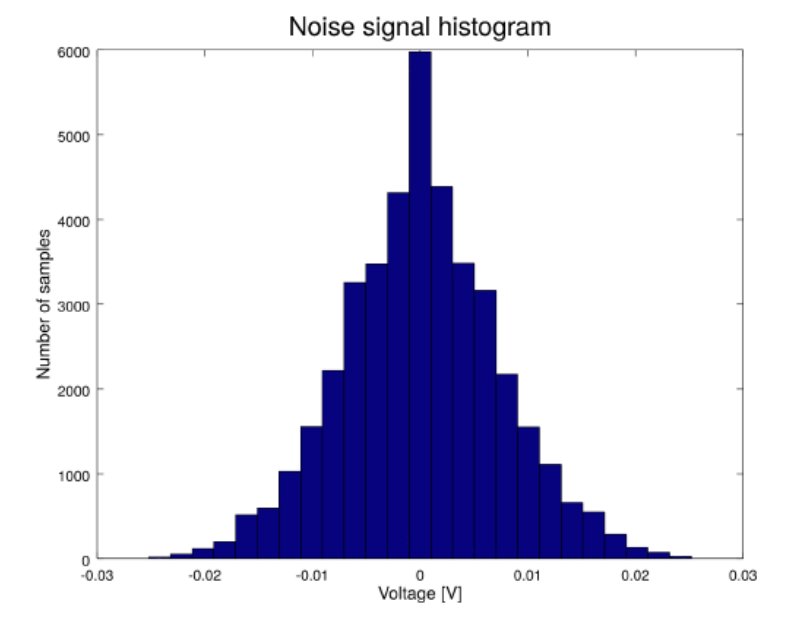 Examplary noise signal histogram of the JUR01 QRNG system component (RIGOL DS1054).
Examplary noise signal histogram of the JUR01 QRNG system component (RIGOL DS1054).
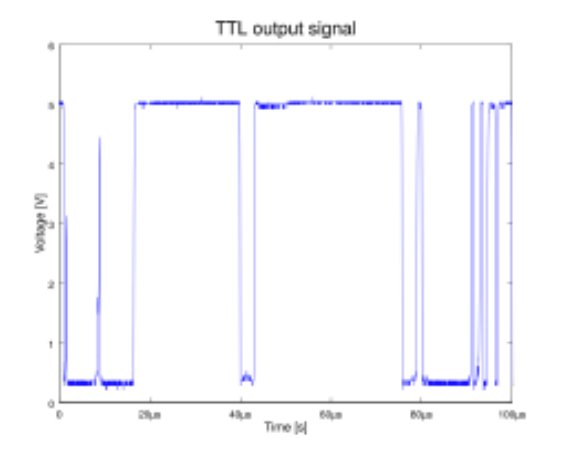 Exemplary TTL at the QRNG system output.
Exemplary TTL at the QRNG system output.
 Exemplary randomness bitmat of the JUR01 QRNG system based on quantum shot noise.
Exemplary randomness bitmat of the JUR01 QRNG system based on quantum shot noise.
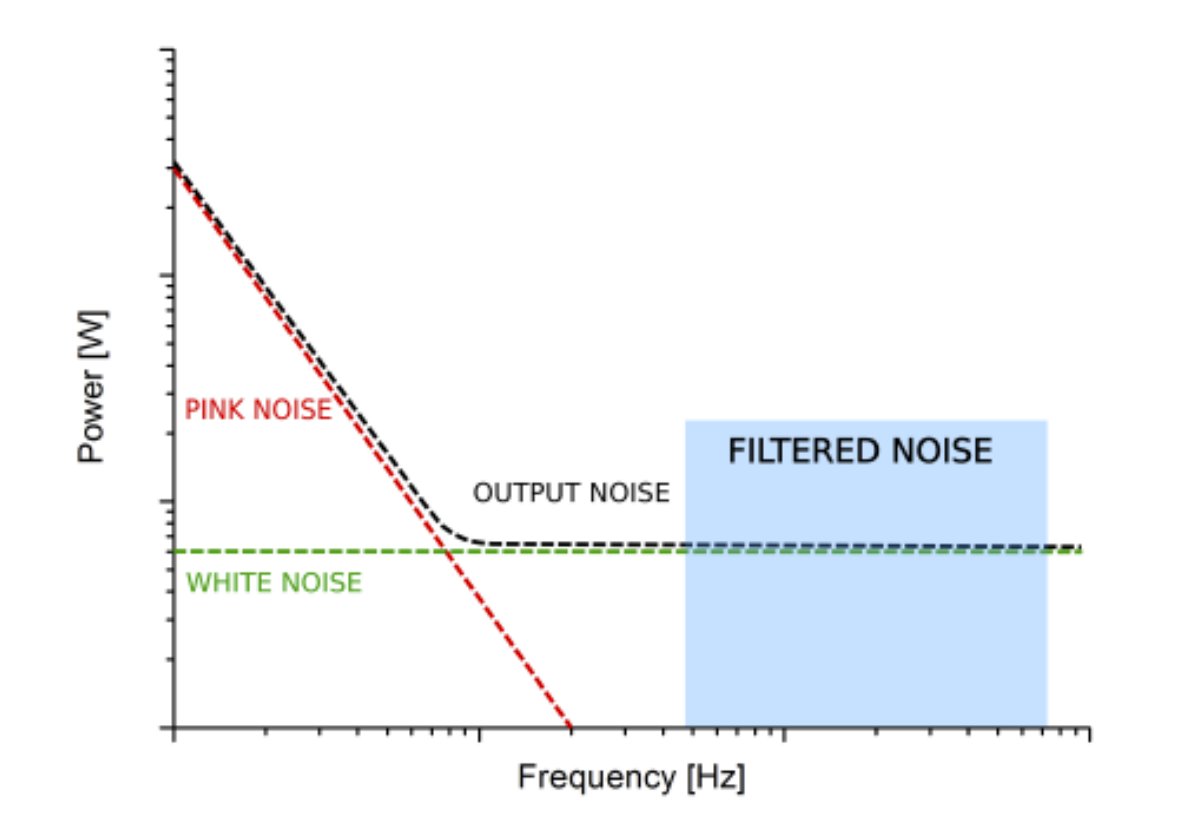 Graph showing different noise components in semiconductors systems with indication for filtering of the shot noise component.
Graph showing different noise components in semiconductors systems with indication for filtering of the shot noise component.
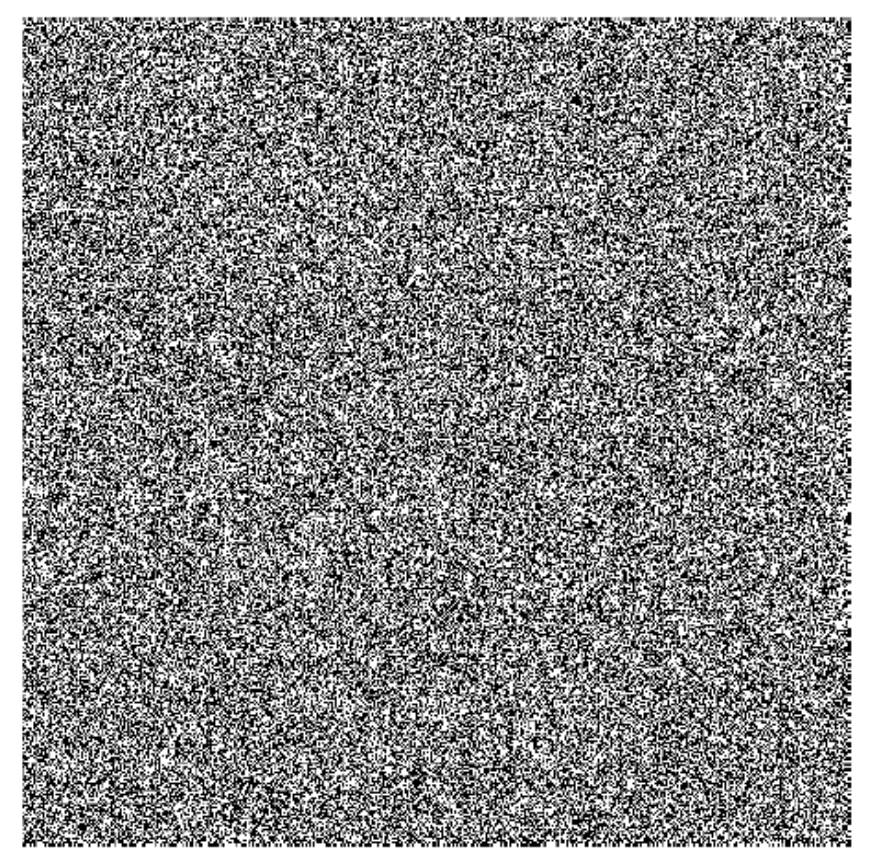 JUR01 QRNG binary randomness generation visualized in a bitmap image showing no patterns of any type.
JUR01 QRNG binary randomness generation visualized in a bitmap image showing no patterns of any type.
OPTICAL TRAP BASED QRNG
 Data acquisition setup for QRNG systems testing.
Data acquisition setup for QRNG systems testing.
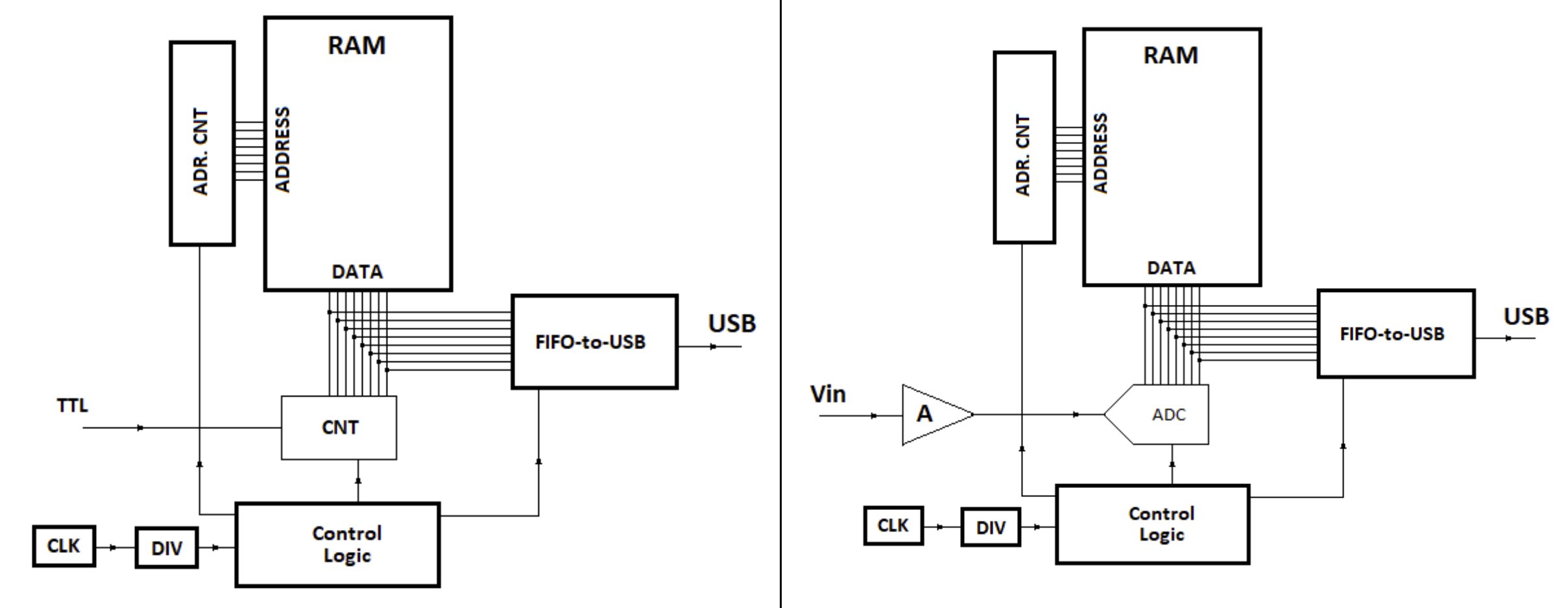 A block schema of the data acquisition setup for QRNG systems testing. A) Impulse counting subsystem. B) Analogue-digital processing subsystem.
A block schema of the data acquisition setup for QRNG systems testing. A) Impulse counting subsystem. B) Analogue-digital processing subsystem.
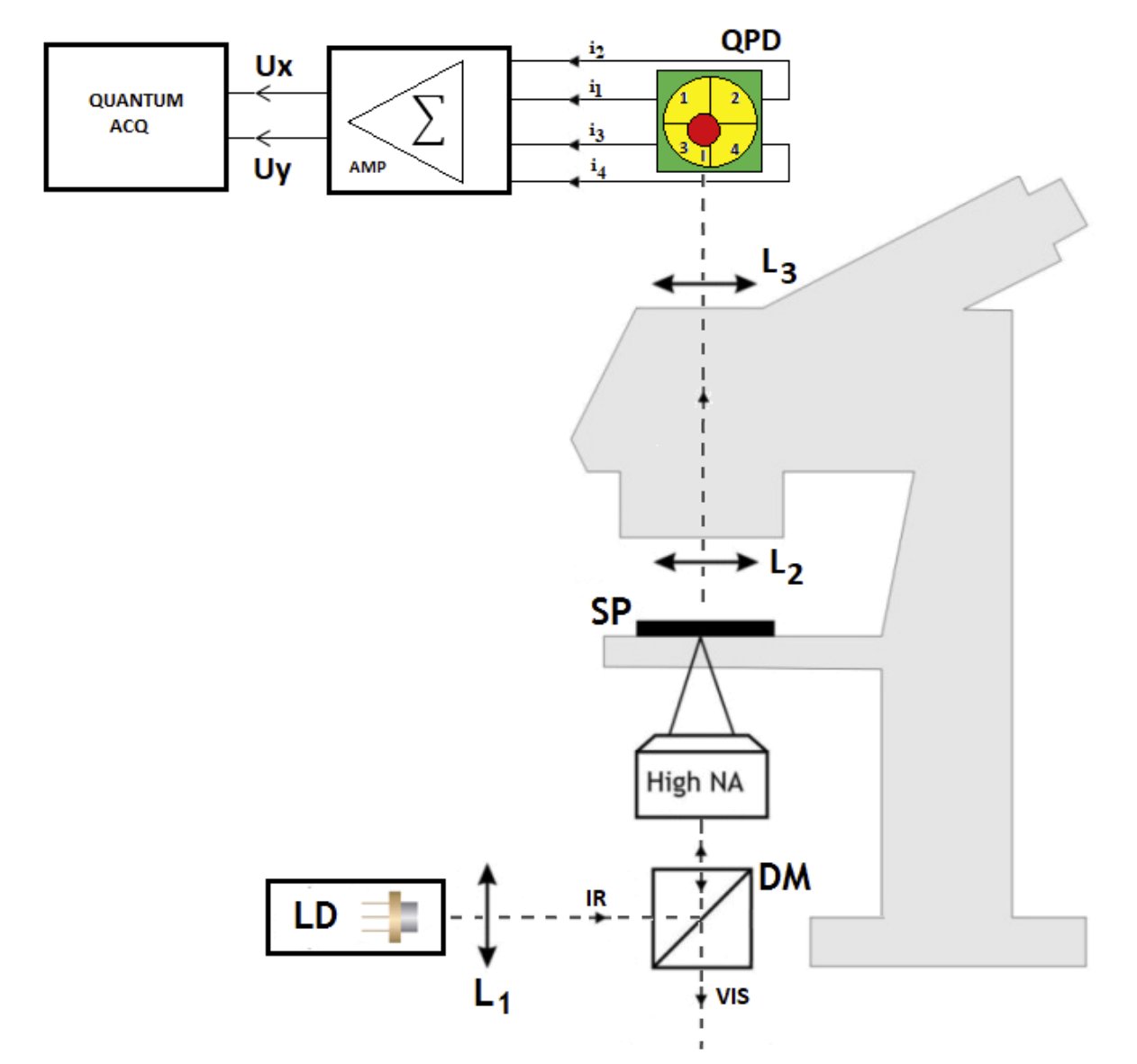 Optical trap QRNG laboratory measurement setup.
Optical trap QRNG laboratory measurement setup.
EITCI QUANTUM STANDARDS GROUP
 Stemming from Consortium for Monitoring of Quantum Cryptography R&D established at the SEQRE 2014 Symposium – https://seqre.net/seqre2014 – the Quantum Standards Group (QSG) hosted by EITCI Institute joins international experts in relevant fields who are interested in quantum technologies standards development, adoption and dissemination. The support of quantum standards specifications in areas such as QKD, QRNG, QC will lead to a faster creation and adoption of such standards by international Standards Developing Organizations leading to a faster uptake of the quantum technology.
The group promotes cooperation in relevant workgroups towards implementation of R&D projects, technological development and deployments focused on defining, supporting and disseminating quantum technology standards. The EITCI QSG activity supports the Quantum Flagship initiative and is a part of the StandICT project of the European Commission Horizon 2020 program.
The list of Members of the EITCI QSG group was last updated on 31st January 2022. The up-to-date listing of the Members can be found at EITCI QSG LinkedIn Group.
Stemming from Consortium for Monitoring of Quantum Cryptography R&D established at the SEQRE 2014 Symposium – https://seqre.net/seqre2014 – the Quantum Standards Group (QSG) hosted by EITCI Institute joins international experts in relevant fields who are interested in quantum technologies standards development, adoption and dissemination. The support of quantum standards specifications in areas such as QKD, QRNG, QC will lead to a faster creation and adoption of such standards by international Standards Developing Organizations leading to a faster uptake of the quantum technology.
The group promotes cooperation in relevant workgroups towards implementation of R&D projects, technological development and deployments focused on defining, supporting and disseminating quantum technology standards. The EITCI QSG activity supports the Quantum Flagship initiative and is a part of the StandICT project of the European Commission Horizon 2020 program.
The list of Members of the EITCI QSG group was last updated on 31st January 2022. The up-to-date listing of the Members can be found at EITCI QSG LinkedIn Group.
 Reference Standard for EQRNG – Theoretical Concepts – RS-EITCI-QSG-EQRNG-THEORY-STD-VER-1.0:
Reference Standard for EQRNG – Theoretical Concepts – RS-EITCI-QSG-EQRNG-THEORY-STD-VER-1.0:
 Reference Standard for EQRNG – Protocols, Processes, Devices and Operative Principles – RS-EITCI-QSG-EQRNG-PROTOCOLS-STD-VER-1.0:
Reference Standard for EQRNG – Protocols, Processes, Devices and Operative Principles – RS-EITCI-QSG-EQRNG-PROTOCOLS-STD-VER-1.0:
 Reference Standard for EQRNG – Testing and Verification Schemes including Sustaining Secrecy – RS-EITCI-QSG-EQRNG-TESTING-STD-VER-1.0:
Reference Standard for EQRNG – Testing and Verification Schemes including Sustaining Secrecy – RS-EITCI-QSG-EQRNG-TESTING-STD-VER-1.0:
SEQRE PATENT APPLICATIONS
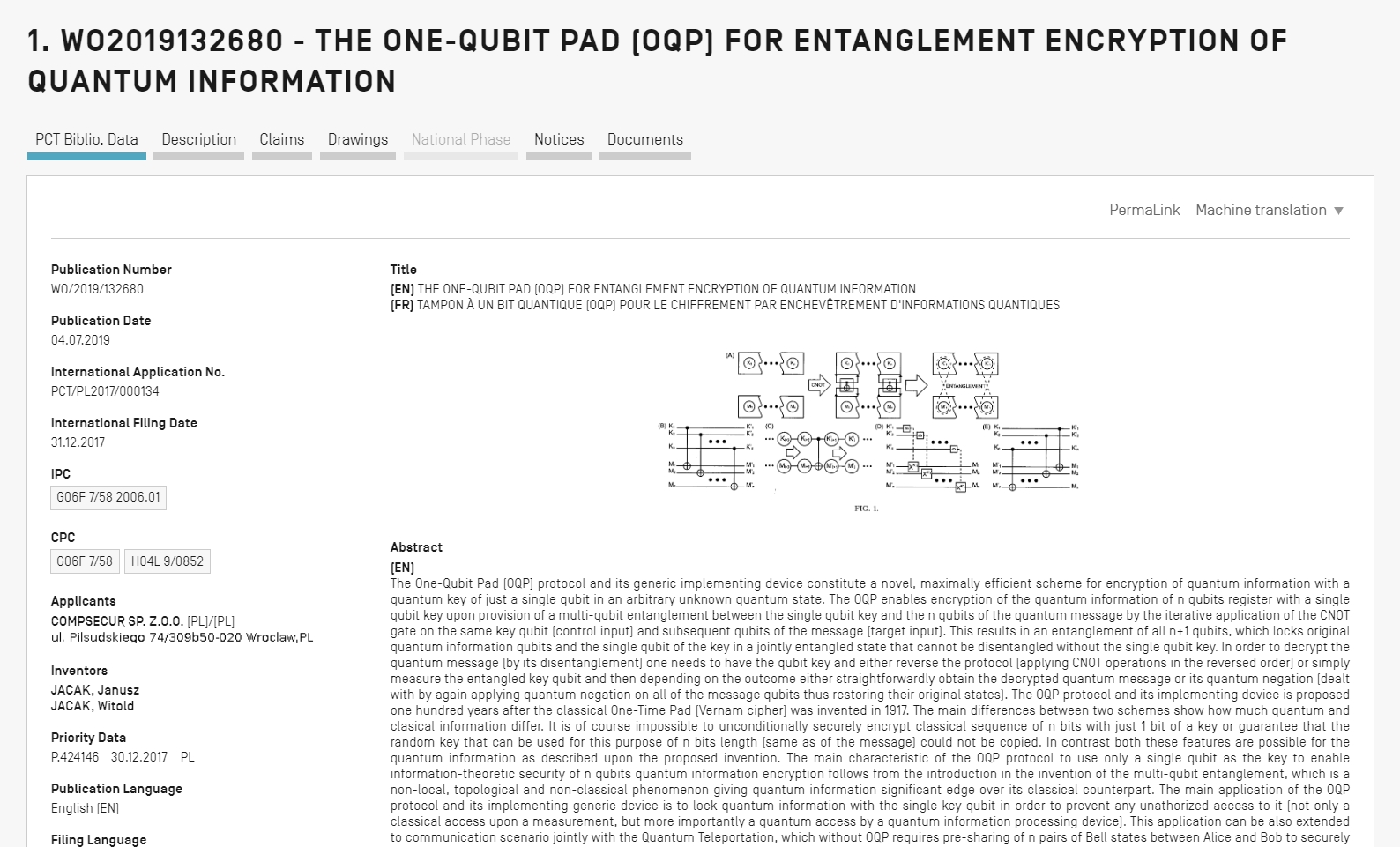
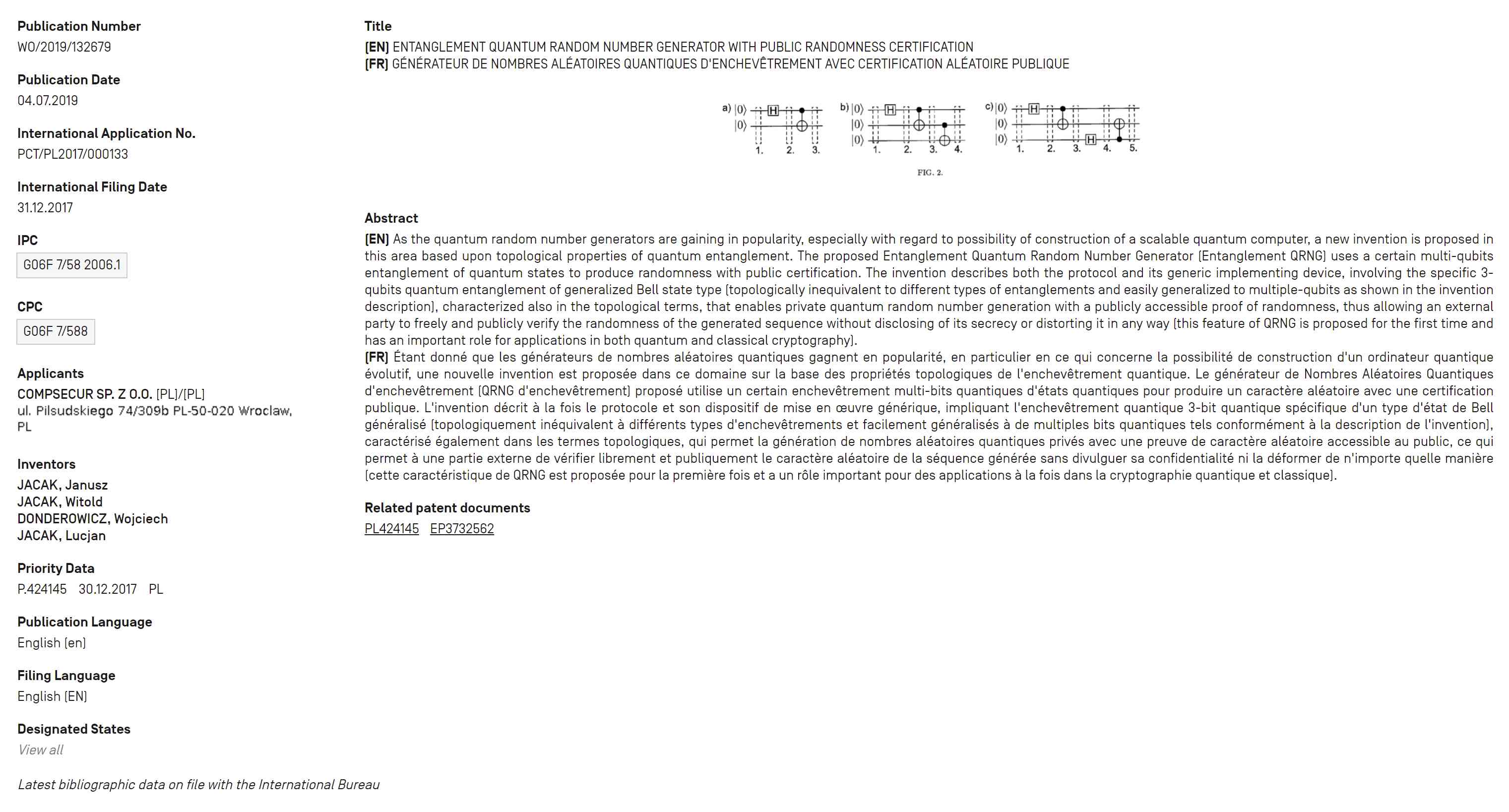
Patenting of novel hardware and protocol technical solutions is a key element of the Quantum Cryptography commercialization efforts. The R&D carried out resulted in the following two new quantum systems patents: Entanglement Quantum Random Number Generator With Public Randomness Certification (WIPO PCT Patent):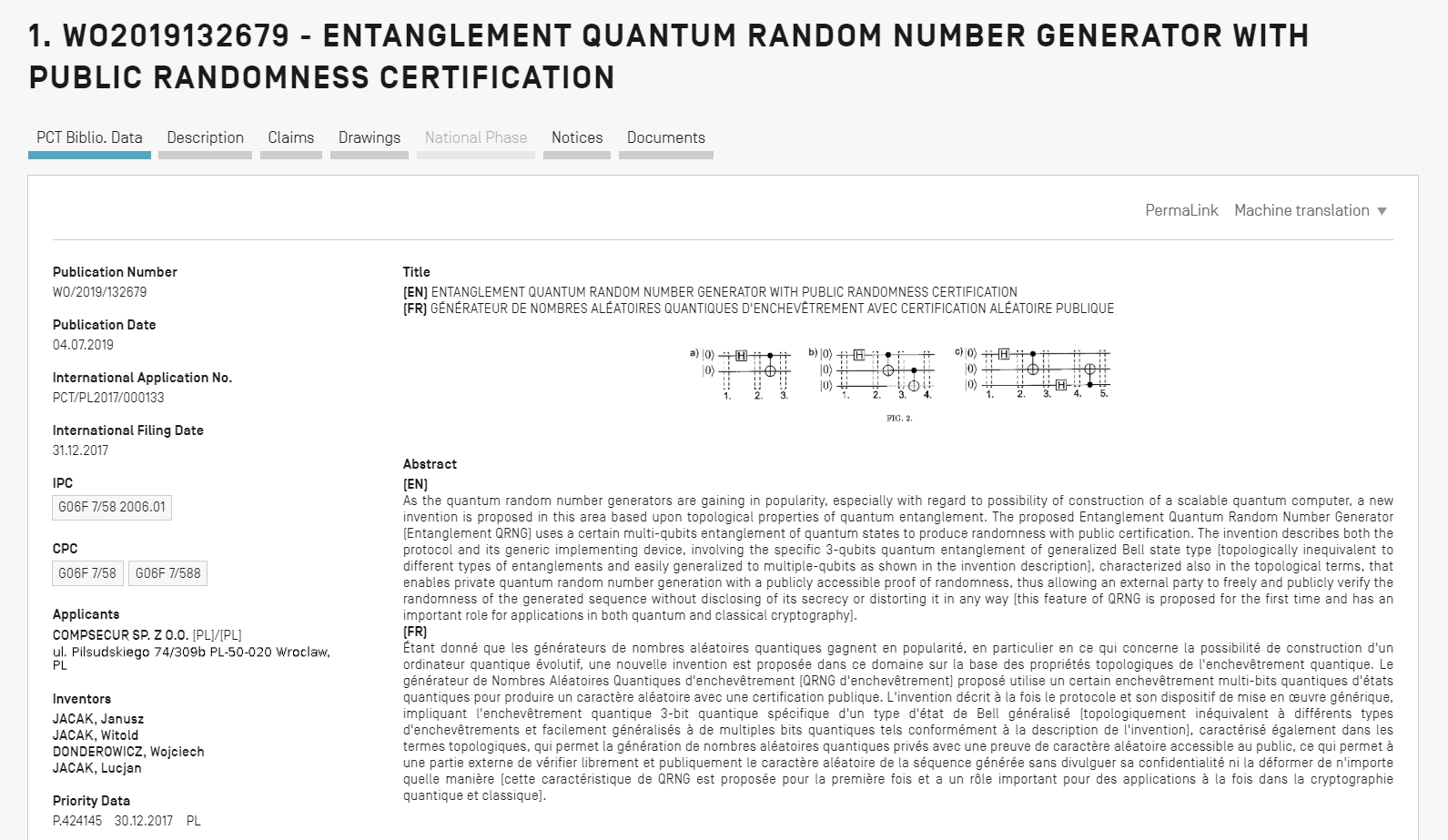 The One-Qubit Pad (OQP) for Entanglement Encryption of Quantum Information (WIPO PCT Patent):
The One-Qubit Pad (OQP) for Entanglement Encryption of Quantum Information (WIPO PCT Patent):
 More on development of the Polish national QKD systems:
More on development of the Polish national QKD systems:
 Examplary seQre QKD system deployed in standardized network server rack architecture:
Examplary seQre QKD system deployed in standardized network server rack architecture:

MOST IMPORTANT QRNG PROJECT PUBLICATIONS
“Quantum random number generator protocols based on topologically inequivalent entanglements of quantum states”, Entropy – Open Access Journal, ISSN 1099-4300, MDPI: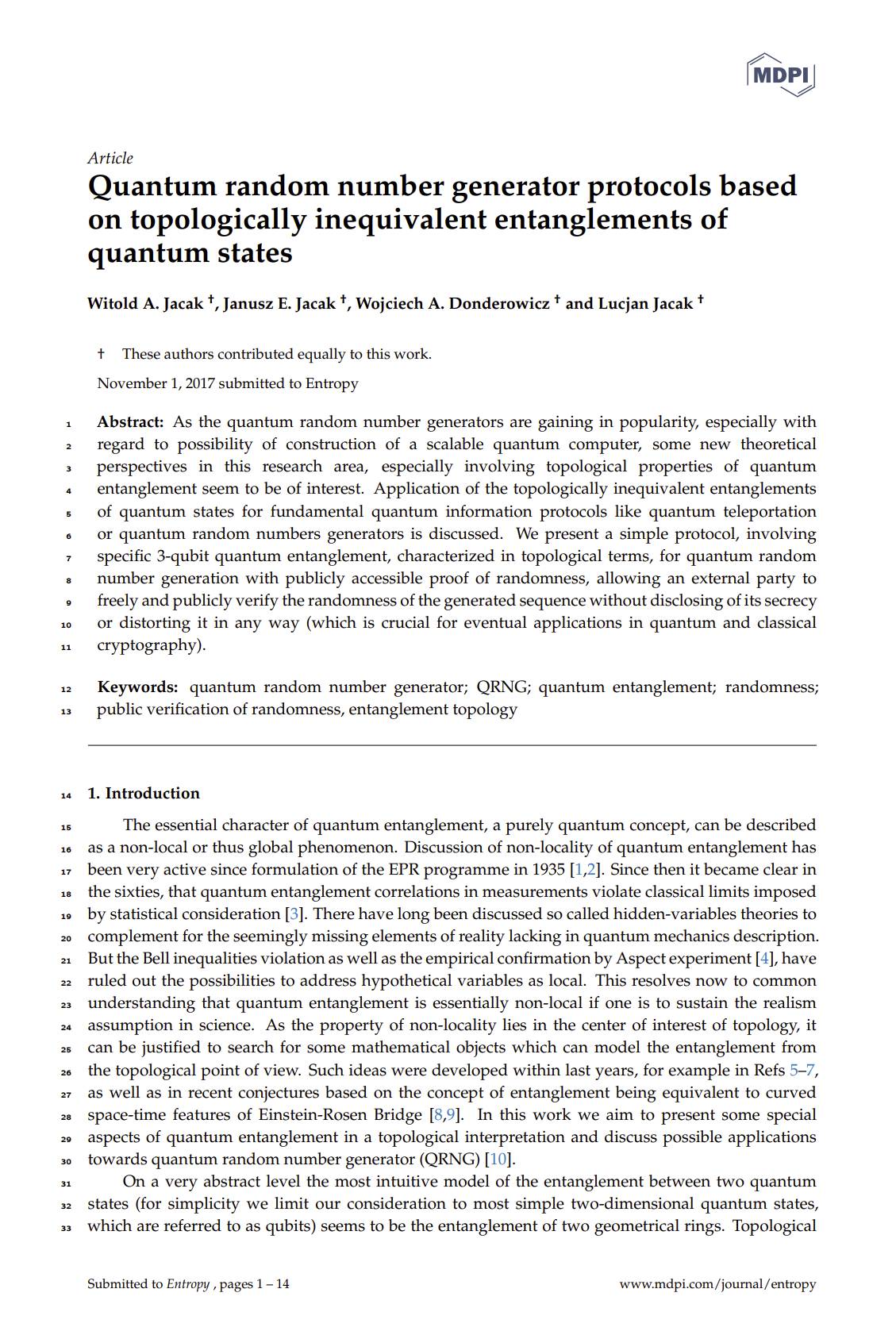 “Randomness”, SeQre.net:
“Randomness”, SeQre.net:
 “Random numbers generator statistical tests”, SeQre.net:
“Random numbers generator statistical tests”, SeQre.net:
 “Entanglement Quantum Random Number Generator with public randomness certification” Patent application (international PCT procedure, application no: WIPO ST 10/CPL424140 of 31.12.2017):
“Entanglement Quantum Random Number Generator with public randomness certification” Patent application (international PCT procedure, application no: WIPO ST 10/CPL424140 of 31.12.2017):
 “Beam splitter and polarization beam splitter quantitative testing”, SeQre.net:
“Beam splitter and polarization beam splitter quantitative testing”, SeQre.net:
 “Quantum random number generators with entanglement for public randomness testing”, January 13, 2020, Scientific Reports, Nature Springer:
“Quantum random number generators with entanglement for public randomness testing”, January 13, 2020, Scientific Reports, Nature Springer:
 “Quantum generators of random numbers”, August 9, 2021, Scientific Reports, Nature Springer:
“Quantum generators of random numbers”, August 9, 2021, Scientific Reports, Nature Springer:
 “Supplementary Information: Quantum generators of random numbers”, August 9, 2021, Scientific Reports, Nature Springer:
“Supplementary Information: Quantum generators of random numbers”, August 9, 2021, Scientific Reports, Nature Springer:
 “Random Quantum Noise Generation Using Shot Noise in Semiconductors”, SeQre.net:
“Random Quantum Noise Generation Using Shot Noise in Semiconductors”, SeQre.net:
 “Quantum Nano-Plasmonics” monograph containing some discussion on aspects of quantum randomness generation in due of nano-plasmonic quantum effects, August 2020, Cambridge University Press:
“Quantum Nano-Plasmonics” monograph containing some discussion on aspects of quantum randomness generation in due of nano-plasmonic quantum effects, August 2020, Cambridge University Press:
 Quantum random number generators with entanglement for public randomness testing while preserving its secrecy for crypto-applications – seQre achievements in QRNG:
Quantum random number generators with entanglement for public randomness testing while preserving its secrecy for crypto-applications – seQre achievements in QRNG: